Are you looking for a reliable way to remotely access IoT devices using SSH and web interfaces on your Android device? You're in the right place. The Internet of Things (IoT) has revolutionized the way we interact with technology, enabling us to control and monitor devices from anywhere in the world. However, accessing these devices securely and efficiently requires the right tools and knowledge. In this article, we’ll explore how you can remotely access IoT devices using SSH and web interfaces on Android, ensuring a seamless and secure connection.
Remote access to IoT devices is essential for managing smart homes, industrial automation, and various other applications. Whether you're a developer, IT professional, or simply a tech enthusiast, understanding how to securely access IoT devices remotely is a valuable skill. With the increasing number of IoT devices being deployed globally, the need for secure and efficient remote access has never been more critical. This guide will provide you with step-by-step instructions, tools, and best practices to ensure you can manage your IoT devices with confidence.
In this article, we’ll cover everything from the basics of IoT remote access to advanced techniques using SSH and web interfaces on Android. We’ll also discuss the importance of security, provide practical examples, and recommend trusted tools to help you get started. By the end of this guide, you’ll have a comprehensive understanding of how to remotely access IoT devices securely and efficiently, empowering you to take full control of your smart devices.
Read also:Jeff Allen Comedian Net Worth A Comprehensive Guide To His Career And Financial Success
Table of Contents
- Introduction to Remote Access for IoT Devices
- Understanding SSH for IoT Device Management
- Web-Based Access to IoT Devices
- Top Android Tools for Remote IoT Access
- Step-by-Step Guide to Access IoT Devices via SSH on Android
- Security Best Practices for Remote IoT Access
- Advanced Techniques for IoT Remote Management
- Troubleshooting Tips for Common Issues
- Real-World Examples of IoT Remote Access
- Conclusion and Call to Action
Introduction to Remote Access for IoT Devices
Remote access to IoT devices allows users to monitor and control their devices from a distance, providing convenience and flexibility. This capability is particularly useful for managing smart home devices, industrial sensors, and other connected systems. By leveraging remote access, users can troubleshoot issues, update firmware, and retrieve data without being physically present.
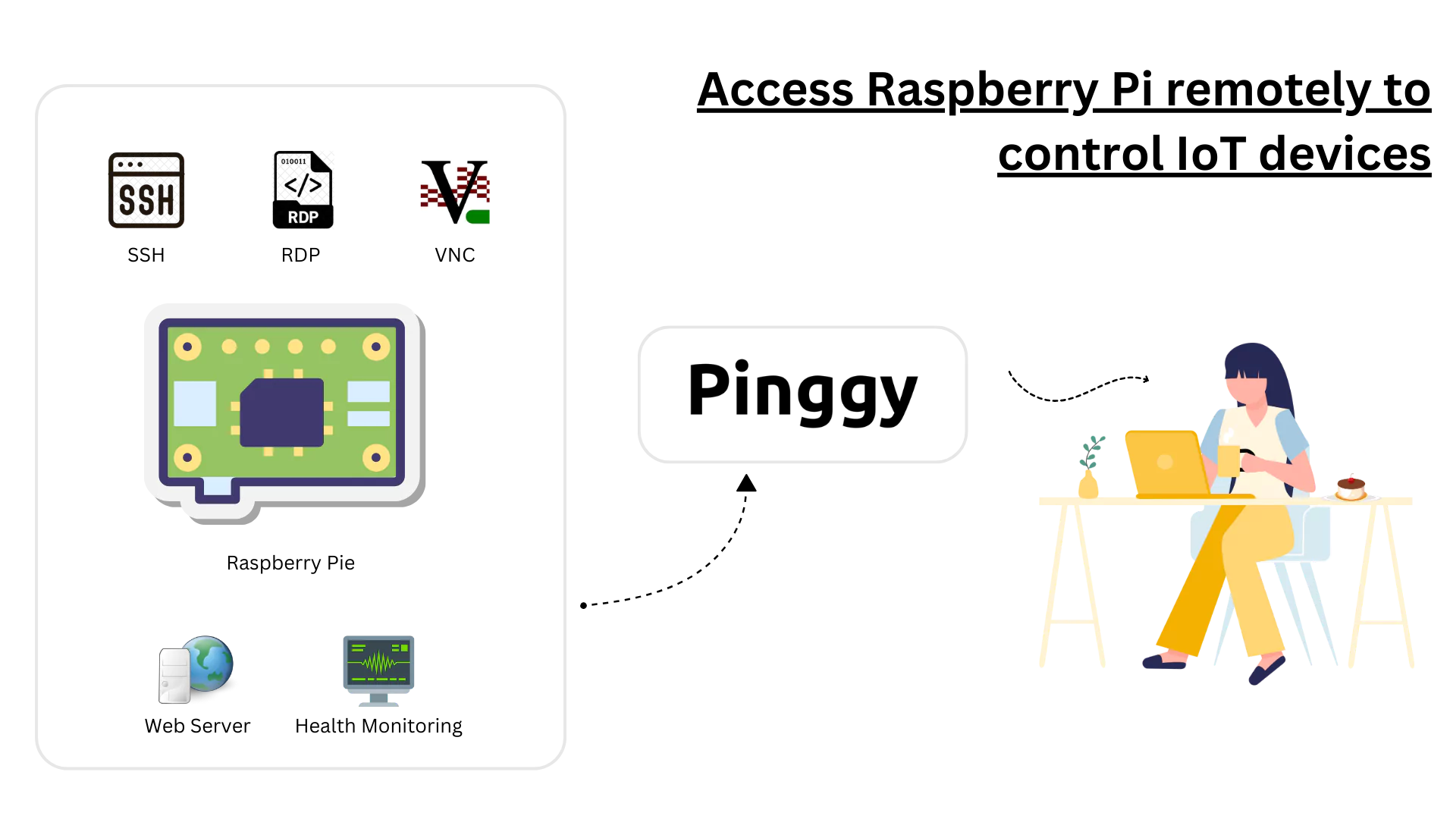
There are several methods to achieve remote access, including SSH (Secure Shell) and web-based interfaces. SSH is a protocol that provides a secure channel for communication between devices, while web-based interfaces allow users to interact with IoT devices through a browser. Both methods have their advantages, and the choice depends on the specific requirements of the user and the device.
When accessing IoT devices remotely, it’s crucial to prioritize security. Unauthorized access can lead to data breaches, device malfunction, or even physical damage. Therefore, implementing robust security measures, such as strong passwords, encryption, and two-factor authentication, is essential. In the following sections, we’ll delve deeper into these methods and explore how you can use them effectively on Android devices.
Understanding SSH for IoT Device Management
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication between devices. It is widely regarded as one of the most secure methods for remote access due to its encryption capabilities. When managing IoT devices, SSH allows users to execute commands, transfer files, and configure settings securely.
How SSH Works
SSH operates on a client-server model, where the client (your Android device) connects to the server (the IoT device). The connection is encrypted, ensuring that data transmitted between the devices cannot be intercepted by unauthorized parties. SSH also supports key-based authentication, which is more secure than traditional password-based methods.
Advantages of Using SSH for IoT Devices
- Security: SSH encrypts all data, protecting it from eavesdropping and tampering.
- Flexibility: SSH can be used for various tasks, including file transfers and remote command execution.
- Compatibility: Most IoT devices support SSH, making it a versatile option for remote access.
Setting Up SSH on IoT Devices
To use SSH for IoT device management, you need to enable SSH on the device and configure it to accept connections. This typically involves installing an SSH server on the IoT device and configuring firewall rules to allow SSH traffic. Once set up, you can use an SSH client on your Android device to connect to the IoT device securely.
Read also:Jenny Slate And Her Stance On Israel A Comprehensive Guide
Web-Based Access to IoT Devices
Web-based access provides an alternative method for managing IoT devices remotely. This approach involves accessing a web interface hosted on the IoT device through a browser on your Android device. Web-based interfaces are user-friendly and often include features such as dashboards, configuration panels, and real-time data visualization.
Advantages of Web-Based Access
- User-Friendly: Web interfaces are intuitive and easy to navigate, even for non-technical users.
- Real-Time Monitoring: Many web-based interfaces provide real-time data and analytics, enabling quick decision-making.
- Cross-Platform Compatibility: Web interfaces can be accessed from any device with a browser, making them highly versatile.
Securing Web-Based Access
While web-based access is convenient, it also introduces potential security risks. To mitigate these risks, ensure that the web interface is protected by strong authentication mechanisms, such as HTTPS encryption and two-factor authentication. Regularly updating the firmware of the IoT device is also crucial to address any vulnerabilities.
Top Android Tools for Remote IoT Access
There are several Android applications available that make remote IoT access seamless and efficient. These tools support SSH, web-based access, and other protocols, providing users with a variety of options to suit their needs.
Termius
Termius is a popular SSH client for Android that offers a user-friendly interface and robust features. It supports key-based authentication, multi-device synchronization, and secure file transfers. Termius is ideal for users who need a reliable and secure way to manage IoT devices remotely.
ConnectBot
ConnectBot is an open-source SSH client for Android that provides a lightweight and efficient solution for remote access. It supports multiple simultaneous connections, making it suitable for managing multiple IoT devices at once. ConnectBot is a great choice for users who prefer open-source software.
HTTP Injector
HTTP Injector is a versatile tool that allows users to access web-based interfaces securely. It supports SSH tunneling, which can be used to encrypt web traffic and protect sensitive data. HTTP Injector is particularly useful for users who need to access IoT devices through restricted networks.
Step-by-Step Guide to Access IoT Devices via SSH on Android
Accessing IoT devices via SSH on Android is a straightforward process, provided you have the right tools and configuration. Follow these steps to establish a secure SSH connection:
Step 1: Enable SSH on the IoT Device
Before you can connect to an IoT device via SSH, you need to enable SSH on the device. This typically involves installing an SSH server and configuring it to accept connections. Refer to the device’s documentation for specific instructions.
Step 2: Install an SSH Client on Android
Download and install an SSH client app, such as Termius or ConnectBot, from the Google Play Store. These apps provide a user-friendly interface for managing SSH connections.
Step 3: Connect to the IoT Device
Open the SSH client app and enter the IoT device’s IP address, username, and password. If using key-based authentication, upload the private key to the app. Once connected, you can execute commands and manage the device remotely.
Step 4: Secure the Connection
Ensure that the SSH connection is encrypted and that strong authentication methods are in place. Regularly update the IoT device’s firmware and SSH client app to address any security vulnerabilities.
Security Best Practices for Remote IoT Access
Securing remote access to IoT devices is critical to prevent unauthorized access and data breaches. Follow these best practices to ensure your IoT devices remain secure:
Use Strong Passwords
Always use strong, unique passwords for SSH and web-based access. Avoid using default passwords, as they are often targeted by attackers.
Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide a second form of verification, such as a code sent to their phone.
Regularly Update Firmware
Keep the IoT device’s firmware up to date to address any security vulnerabilities. Manufacturers often release updates to patch known issues and improve security.
Advanced Techniques for IoT Remote Management
For users who require more advanced remote management capabilities, there are several techniques and tools available:
SSH Tunneling
SSH tunneling allows you to encrypt web traffic and access IoT devices securely through restricted networks. This technique is particularly useful for users who need to bypass firewalls or access devices behind NAT.
Automating Tasks with Scripts
Automating repetitive tasks using scripts can save time and improve efficiency. Tools like Python and Bash can be used to write scripts that execute commands on IoT devices via SSH.
Monitoring and Alerts
Implementing monitoring and alert systems can help you stay informed about the status of your IoT devices. Tools like Nagios and Prometheus can be used to monitor device performance and send alerts when issues arise.
Troubleshooting Tips for Common Issues
Remote access to IoT devices can sometimes encounter issues. Here are some common problems and their solutions:
Connection Failures
If you’re unable to connect to an IoT device, check the device’s IP address, firewall settings, and SSH configuration. Ensure that the SSH server is running and that the correct port is open.
Slow Performance
Slow performance can be caused by network congestion or high device load. Optimize your network settings and ensure that the IoT device has sufficient resources to handle the workload.
Authentication Errors
If you’re experiencing authentication errors, verify that you’re using the correct username and password. If using key-based authentication, ensure that the private key is correctly configured.
Real-World Examples of IoT Remote Access
Remote access to IoT devices is used in a variety of industries and applications. Here are some real-world examples:
Smart Home Automation
Homeowners use remote access to control smart thermostats, lighting, and security systems. This allows them to manage their homes efficiently and save energy.
Industrial Automation
Manufacturers use remote access to monitor and control industrial sensors and machinery. This enables them to optimize production processes and reduce downtime.
Healthcare Monitoring
Healthcare providers use remote access to monitor patients’ vital signs and medical devices. This allows them to provide timely care and improve patient outcomes.
Conclusion and Call to Action
Remote access to IoT devices via SSH and web interfaces on Android is a powerful capability that can enhance convenience, efficiency, and security. By following the steps and best practices outlined in this guide, you can confidently manage your IoT devices from anywhere in the world. Whether you’re a developer, IT professional, or tech enthusiast, mastering remote IoT access is a valuable skill that will serve you well in the era of connected devices.
We encourage you to share your experiences and insights in the comments below. Have you encountered any challenges while remotely accessing IoT devices? Do you have any tips or tools to recommend? Your input can help others in the community improve their remote management strategies. Don’t forget to share this article with your network and explore other resources on our site for more valuable insights into IoT and remote access technologies.