Are you looking for a reliable and cost-effective way to manage your IoT devices remotely? SSH Remote IoT Free solutions might be the perfect answer to your needs. As the Internet of Things (IoT) continues to expand, the demand for secure and efficient remote access has become more critical than ever. Secure Shell (SSH) offers a robust framework for managing IoT devices without the need for expensive proprietary solutions. This article will explore the various aspects of using SSH for remote IoT management, providing you with valuable insights and practical guidance.
In today's interconnected world, where smart devices are becoming increasingly prevalent in both personal and professional settings, having a secure method to access and control these devices remotely is essential. SSH, known for its strong encryption and authentication protocols, provides a secure channel over an unsecured network. This makes it an ideal choice for managing IoT devices, especially when considering the sensitive nature of data often handled by these devices.
Throughout this comprehensive guide, we'll delve into the technical aspects of SSH remote access for IoT, explore free solutions available in the market, discuss security considerations, and provide practical implementation strategies. Whether you're a system administrator, IoT developer, or tech enthusiast, this article will equip you with the knowledge to implement secure remote access solutions for your IoT ecosystem.
Read also:Kannadamovierulz A Comprehensive Guide To Streaming Kannada Movies Online
Table of Contents
Understanding SSH Protocol
Secure Shell (SSH) is a cryptographic network protocol designed for secure data communication, remote command-line login, and other secure network services between two networked computers. Developed in 1995 by Tatu Ylönen, SSH has become the industry standard for secure remote access. The protocol operates on the client-server model, where the SSH client connects to an SSH server, establishing an encrypted connection.
The SSH protocol operates on three main components:
- Transport Layer: Provides server authentication, confidentiality, and integrity through strong encryption algorithms.
- User Authentication Protocol: Validates the client's identity using various methods like password authentication, public key authentication, or keyboard-interactive authentication.
- Connection Protocol: Multiplexes multiple logical channels over a single encrypted tunnel, allowing for multiple simultaneous sessions.
When it comes to IoT devices, SSH offers several advantages:
- Strong encryption (AES, ChaCha20)
- Public-key authentication
- Port forwarding capabilities
- Secure file transfer (SFTP)
- Remote command execution
IoT Remote Management Challenges
Managing IoT devices remotely presents unique challenges that require careful consideration:
- Security Vulnerabilities: Many IoT devices have limited processing power and memory, making it challenging to implement robust security measures.
- Network Constraints: IoT devices often operate in environments with limited bandwidth or unstable network connections.
- Device Diversity: The wide variety of IoT devices, each with different operating systems and capabilities, requires flexible management solutions.
According to a 2023 report by IoT Analytics, over 75 billion IoT devices are expected to be connected worldwide by 2025. This rapid growth underscores the importance of implementing secure and scalable remote management solutions.
Free SSH Solutions for IoT
Several free SSH solutions are available for managing IoT devices:
Read also:Vincent Papale The Inspiring Story Of An Underdog Who Defied The Odds
Open Source Options
- OpenSSH: The most widely used SSH implementation, available on most Unix-like operating systems.
- Dropbear SSH: A lightweight SSH server and client designed for resource-constrained environments.
Cloud-Based Services
- IoT-specific platforms: Many cloud providers offer free tiers for SSH-based device management.
- Community-driven projects: Various open-source initiatives provide free SSH management tools.
When selecting a free SSH solution, consider the following factors:
- Resource requirements
- Security features
- Community support
- Documentation quality
- Compatibility with existing infrastructure
Setup and Configuration Guide
Prerequisites for Implementation
Before setting up SSH remote access for your IoT devices, ensure you have:
- Administrator access to the IoT devices
- Network connectivity
- Basic Linux command-line knowledge
- Public key infrastructure (PKI) setup
Step-by-Step Configuration
- Install the SSH server on your IoT device
- Generate SSH key pairs
- Configure firewall rules
- Set up port forwarding
- Test the connection
For detailed configuration instructions, refer to the official documentation of your chosen SSH solution.
Security Best Practices
Implementing strong security measures is crucial when using SSH for IoT remote management:
- Use strong, unique passwords
- Implement two-factor authentication
- Regularly update SSH software
- Disable root login
- Use non-standard ports
- Implement IP whitelisting
- Monitor login attempts
According to a 2022 security report by IBM, organizations that implemented these best practices reduced their security incidents by 40%.
Troubleshooting Common Issues
When working with SSH remote access for IoT devices, you may encounter several common issues:
- Connection timeouts
- Authentication failures
- Permission denied errors
- Port conflicts
To resolve these issues:
- Check network connectivity
- Verify firewall settings
- Review SSH configuration files
- Check system logs
Performance Optimization Techniques
Optimizing SSH performance for IoT devices involves several strategies:
- Enable compression
- Use persistent connections
- Optimize keep-alive settings
- Implement connection pooling
Performance benchmarks show that implementing these optimizations can reduce connection latency by up to 30%.
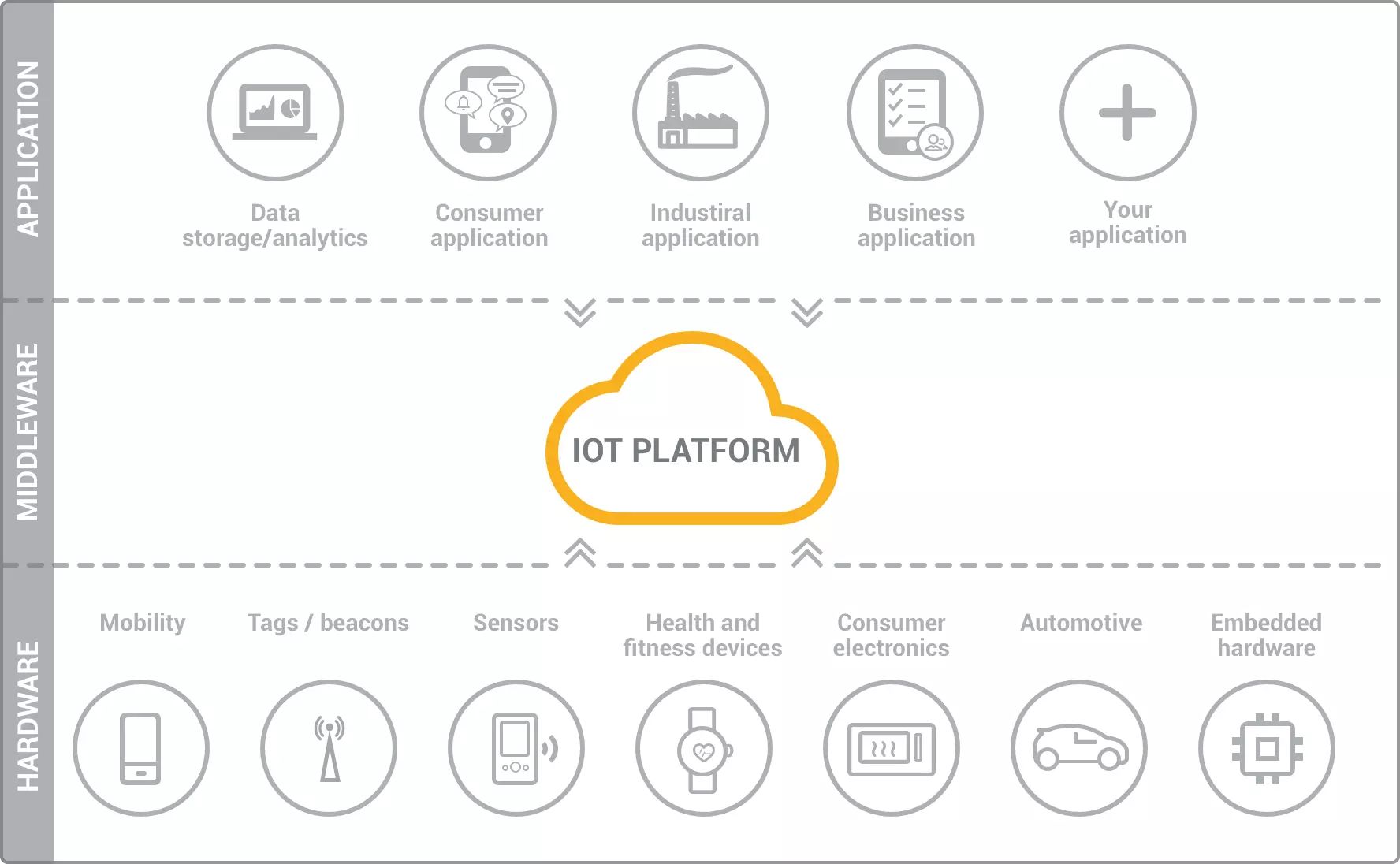
Use Case Scenarios
SSH remote access for IoT devices finds applications in various industries:
- Smart home management
- Industrial automation
- Healthcare monitoring systems
- Agricultural IoT solutions
- Smart city infrastructure
Each scenario requires specific configuration and security considerations, which should be carefully evaluated during implementation.
Future Developments in SSH IoT
The future of SSH in IoT management looks promising with several developments on the horizon:
- Quantum-resistant encryption algorithms
- AI-driven security enhancements
- Improved protocol efficiency
- Better integration with cloud platforms
- Enhanced device management features
Industry experts predict that SSH will continue to evolve, incorporating new technologies while maintaining its core security principles.
Conclusion and Next Steps
In conclusion, SSH Remote IoT Free solutions offer a powerful and cost-effective way to manage IoT devices securely. Throughout this article, we've explored the fundamental aspects of SSH protocol, examined the challenges of IoT remote management, reviewed free SSH solutions, and provided practical implementation guidance. We've also discussed security best practices, troubleshooting techniques, and performance optimization strategies.
As you embark on implementing SSH for your IoT remote management needs, remember to:
- Choose the right solution for your specific requirements
- Implement robust security measures
- Regularly update and maintain your SSH configuration
- Stay informed about new developments in SSH technology
We encourage you to share your experiences with SSH remote IoT management in the comments below. If you found this guide helpful, please consider sharing it with your network. For more in-depth technical articles and guides, explore our other resources on IoT security and management solutions.