Are you looking for a reliable way to manage your IoT devices remotely using SSH web access on your Android device? With the increasing number of smart devices in our homes and workplaces, having secure and efficient access to IoT devices is essential. SSH (Secure Shell) is a powerful protocol that allows you to securely access and manage your IoT devices over the internet. In this article, we will explore how you can leverage free Android applications to establish SSH web access for your IoT devices.
The ability to remotely control IoT devices via SSH is not only convenient but also crucial for ensuring their security and functionality. Whether you're a tech enthusiast, a developer, or simply someone who wants to manage their smart devices more effectively, understanding how to set up SSH web access on Android can save you time and effort. This article will guide you through the process step-by-step, ensuring you have all the tools and knowledge needed to get started.
Throughout this guide, we will cover everything from basic concepts to advanced tips for managing IoT devices securely. We will also explore some of the best free Android applications available for SSH access and provide you with actionable insights to enhance your IoT management experience. By the end of this article, you will have a comprehensive understanding of SSH web access and how to implement it effectively.
Read also:Ullu Prime Movierulz A Comprehensive Guide To Streaming And Legal Concerns
Table of Contents
Introduction to SSH Web Access
SSH, or Secure Shell, is a cryptographic network protocol used for secure data communication, remote command execution, and other secure network services between two networked computers. It provides a secure channel over an unsecured network by using a client-server architecture. SSH is widely used by system administrators and developers to manage servers and IoT devices remotely.
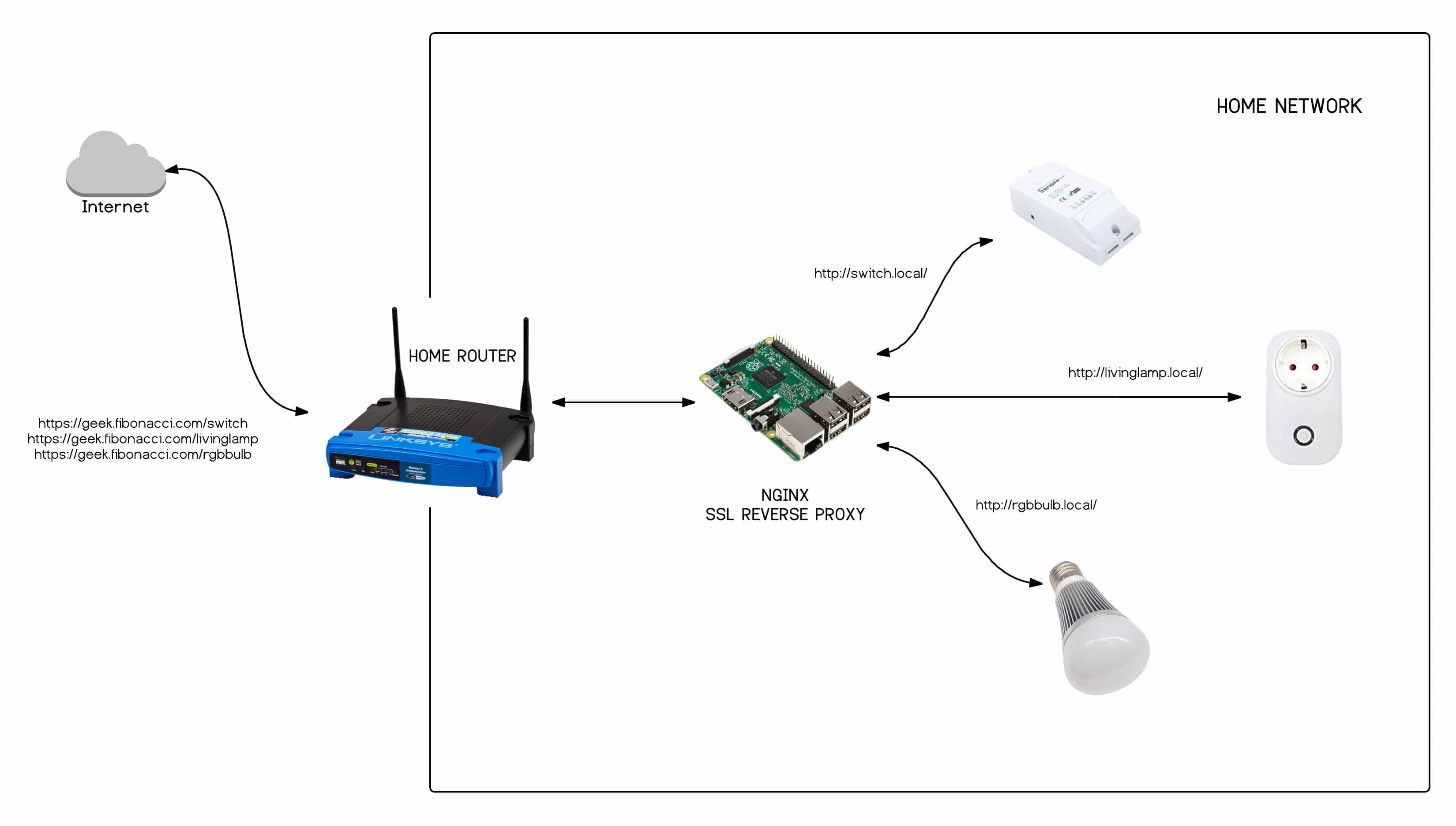
With the rise of IoT devices, the need for secure remote access has become more critical than ever. SSH web access allows you to connect to your IoT devices from anywhere in the world, provided you have an internet connection. This capability is particularly useful for managing devices that are located in remote or inaccessible locations.
Why Use SSH for IoT Devices?
SSH offers several advantages for managing IoT devices:
- Security: SSH encrypts all data transmitted between the client and the server, ensuring that sensitive information remains protected.
- Flexibility: SSH supports various authentication methods, including password-based and key-based authentication.
- Efficiency: SSH allows you to execute commands remotely, making it easier to manage multiple devices simultaneously.
Benefits of SSH for IoT Devices
Using SSH for IoT devices offers numerous benefits that enhance both security and functionality. Here are some of the key advantages:
Enhanced Security
One of the primary reasons to use SSH for IoT devices is the enhanced security it provides. Unlike other protocols, SSH encrypts all data transmitted between the client and the server, making it difficult for attackers to intercept and decipher the information. This encryption ensures that your IoT devices remain protected from unauthorized access and potential cyber threats.
Remote Management
SSH allows you to manage your IoT devices remotely, which is particularly beneficial if you have devices located in different parts of the world. With SSH web access, you can execute commands, update software, and troubleshoot issues without needing physical access to the devices. This capability saves time and resources, making it an ideal solution for managing large-scale IoT deployments.
Read also:Masa49cc A Comprehensive Guide To Understanding And Utilizing This Platform
Automation and Scripting
SSH supports automation and scripting, enabling you to automate repetitive tasks and streamline device management. You can write scripts to perform routine maintenance tasks, such as backups and updates, and execute them remotely via SSH. This automation not only improves efficiency but also reduces the risk of human error.
Top Free Android Apps for SSH Access
There are several free Android applications available that allow you to establish SSH web access for your IoT devices. These apps provide a user-friendly interface and robust features to ensure secure and efficient remote management. Here are some of the top options:
Termius
Termius is a popular SSH client for Android that offers a clean and intuitive interface. It supports key-based authentication, multiple connections, and cloud synchronization, making it an excellent choice for managing IoT devices.
ConnectBot
ConnectBot is another widely used SSH client for Android. It provides a simple and straightforward interface, along with features like port forwarding and multiple sessions. ConnectBot is open-source, ensuring transparency and security.
JuiceSSH
JuiceSSH is a feature-rich SSH client that supports themes, keyboard shortcuts, and secure key storage. It also offers a team collaboration feature, allowing multiple users to manage IoT devices securely.
How to Set Up SSH on Android
Setting up SSH on your Android device is a straightforward process. Follow these steps to establish SSH web access for your IoT devices:
Step 1: Install an SSH Client
Begin by downloading and installing a reliable SSH client from the Google Play Store. Some of the top options include Termius, ConnectBot, and JuiceSSH. Once installed, open the app and familiarize yourself with its interface.
Step 2: Configure SSH Settings
Next, configure the SSH settings by entering the IP address, port number, and authentication details of your IoT device. You can choose between password-based or key-based authentication, depending on your security preferences.
Step 3: Establish a Connection
Once the settings are configured, establish a connection to your IoT device by clicking the "Connect" button. If everything is set up correctly, you should be able to access the device's command line interface and execute commands remotely.
Securing Your SSH Connection
Ensuring the security of your SSH connection is crucial to protect your IoT devices from potential threats. Here are some tips to enhance the security of your SSH connection:
Use Key-Based Authentication
Key-based authentication is more secure than password-based authentication. Generate an SSH key pair and configure your IoT device to use the public key for authentication. This method eliminates the risk of brute-force attacks and ensures that only authorized users can access the device.
Disable Root Login
Disabling root login is another effective way to enhance security. By restricting root access, you reduce the risk of unauthorized users gaining full control over your IoT device. Instead, create a separate user account with limited privileges for SSH access.
Implement Firewall Rules
Implementing firewall rules can help protect your IoT device from unauthorized access. Configure your firewall to allow SSH connections only from trusted IP addresses and block all other incoming traffic. This measure adds an extra layer of security to your SSH connection.
Troubleshooting Common SSH Issues
While SSH is a reliable protocol, you may encounter some common issues when setting up or using it. Here are some troubleshooting tips to help you resolve these issues:
Connection Refused
If you receive a "Connection Refused" error, ensure that the SSH service is running on your IoT device and that the correct port number is configured. You should also check your firewall settings to ensure that SSH traffic is allowed.
Authentication Failed
An "Authentication Failed" error typically indicates an issue with your login credentials. Double-check your username and password, or verify that the correct SSH key is being used for authentication. If you're using key-based authentication, ensure that the public key is correctly configured on the IoT device.
Slow Connection
A slow SSH connection can be caused by network latency or high server load. To improve performance, try connecting to your IoT device during off-peak hours or optimizing your network settings. You can also enable compression in your SSH client to reduce data transfer times.
Advanced Tips for SSH Management
For those looking to take their SSH management skills to the next level, here are some advanced tips to consider:
Use SSH Config Files
SSH config files allow you to store connection settings for multiple devices in a single file. This feature simplifies the process of managing multiple SSH connections and reduces the risk of configuration errors.
Automate Tasks with Scripts
Automating repetitive tasks with scripts can save time and improve efficiency. Use tools like Bash or Python to write scripts that perform routine maintenance tasks, such as backups and updates, and execute them remotely via SSH.
Monitor SSH Logs
Monitoring SSH logs can help you identify potential security threats and troubleshoot issues. Regularly review your logs to detect unauthorized access attempts and take appropriate action to secure your IoT devices.
Best Practices for IoT Device Security
Securing your IoT devices is essential to protect them from cyber threats. Here are some best practices to follow:
Keep Firmware Updated
Regularly update the firmware on your IoT devices to ensure they have the latest security patches. Manufacturers often release updates to address vulnerabilities and improve device performance.
Use Strong Passwords
Use strong, unique passwords for all your IoT devices and change them regularly. Avoid using default passwords, as they are often easily guessed by attackers.
Enable Two-Factor Authentication
Enabling two-factor authentication adds an extra layer of security to your IoT devices. This feature requires users to provide a second form of verification, such as a code sent to their mobile device, before accessing the device.
Frequently Asked Questions
Here are some frequently asked questions about SSH web access for IoT devices:
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used for secure data communication, remote command execution, and other secure network services between two networked computers.
Why is SSH important for IoT devices?
SSH is important for IoT devices because it provides a secure way to access and manage them remotely, ensuring that sensitive information remains protected from cyber threats.
Can I use SSH on my Android device?
Yes, you can use SSH on your Android device by installing a reliable SSH client from the Google Play Store. Some popular options include Termius, ConnectBot, and JuiceSSH.
Conclusion
SSH web access is an essential tool for managing IoT devices securely and efficiently. By leveraging free Android applications, you can establish a reliable SSH connection and take full control of your IoT devices from anywhere in the world. Throughout this article, we have explored the benefits of SSH, provided a step-by-step guide to setting it up on Android, and offered advanced tips for enhancing your SSH management experience.
We encourage you to implement the best practices outlined in this article to ensure the security and functionality of your IoT devices. If you found this guide helpful, please consider sharing it with others who may benefit from it. Additionally, feel free to leave a comment below with any questions or insights you may have. For more informative articles on IoT and technology, be sure to explore our website.