In today's interconnected world, the Internet of Things (IoT) has revolutionized how we interact with technology. From smart homes to industrial automation, IoT devices have become an integral part of our daily lives. However, managing these devices remotely requires a reliable and secure solution. This is where the concept of remote SSH servers for IoT comes into play. Whether you're a developer, system administrator, or IoT enthusiast, understanding how to leverage the best IoT remote SSH server can significantly enhance your operational efficiency while maintaining robust security.
As IoT ecosystems continue to expand, the need for secure remote access becomes increasingly critical. Remote SSH servers provide a secure channel for managing IoT devices, enabling administrators to execute commands, transfer files, and monitor system performance from anywhere in the world. With the right SSH server implementation, you can ensure both convenience and protection for your IoT infrastructure.
This comprehensive guide will explore the top IoT remote SSH server solutions available today, examining their features, security protocols, and implementation best practices. We'll delve into the technical aspects while maintaining a user-friendly approach, ensuring that both technical experts and beginners can benefit from this valuable information. Whether you're setting up a new IoT network or optimizing your existing infrastructure, this article will provide you'verified, expert-recommended solutions to enhance your remote management capabilities.
Read also:Kylie Kelces Daughter And Down Syndrome A Journey Of Love Acceptance And Awareness
Table of Contents
Understanding IoT Remote SSH
Secure Shell (SSH) has become the gold standard for remote access in IoT environments. Unlike traditional remote access methods, SSH provides encrypted communication channels that protect sensitive data during transmission. The protocol operates on port 22 by default and uses public-key cryptography to authenticate devices and users, making it an ideal solution for managing IoT devices securely.
Key Features of IoT Remote SSH
- End-to-end encryption for all data transfers
- Public-key authentication for enhanced security
- Support for multiple authentication methods
- Port forwarding capabilities for secure tunneling
- Comprehensive logging and monitoring features
When selecting an SSH server for IoT applications, it's crucial to consider factors such as scalability, resource efficiency, and compatibility with various IoT platforms. The best IoT remote SSH server should offer minimal latency while maintaining strong security protocols, ensuring smooth operation even with resource-constrained devices.
Top IoT Remote SSH Servers
OpenSSH
OpenSSH stands as one of the most popular and reliable SSH server solutions for IoT environments. Developed as part of the OpenBSD project, it offers robust security features while maintaining excellent performance on resource-limited devices.
- Pros:
- Open-source and free to use
- Regular security updates and patches
- Extensive community support
- Supports various authentication methods
- Cons:
- Configuration can be complex for beginners
- Requires manual updates in some environments
Dropbear SSH
Specifically designed for embedded systems and resource-constrained environments, Dropbear SSH offers a lightweight alternative to traditional SSH servers.
- Key Features:
- Small memory footprint
- Supports both client and server functionality
- Optimized for low-power devices
- Minimal configuration requirements
Security Best Practices
When implementing an IoT remote SSH server, security should be your top priority. Here are crucial best practices to follow:
Authentication Security
- Disable password authentication and use public-key authentication exclusively
- Implement multi-factor authentication (MFA) where possible
- Regularly rotate SSH keys and update access credentials
- Restrict root login access
Network Security Measures
- Change the default SSH port from 22 to a non-standard port
- Implement IP whitelisting for authorized users
- Use firewalls to restrict access to the SSH server
- Enable fail2ban or similar intrusion prevention systems
According to a 2022 IoT security report by Palo Alto Networks, 98% of all IoT device traffic is unencrypted, highlighting the critical need for secure remote access solutions like SSH. [Source: Palo Alto Networks 2022 IoT Security Report]
Read also:Undress Ai Free A Comprehensive Guide To Understanding Its Features And Ethical Implications
Implementation Guide
Setting up your IoT remote SSH server requires careful planning and execution. Follow these steps to ensure a successful implementation:
Pre-Installation Considerations
- Assess your hardware requirements and device capabilities
- Verify operating system compatibility
- Establish a clear access control policy
- Prepare your network infrastructure
Installation and Configuration
- Install the chosen SSH server software
- Generate SSH key pairs for authentication
- Configure the SSH server settings:
- Set protocol versions
- Define allowed authentication methods
- Configure logging parameters
- Test the connection from multiple devices
- Implement monitoring tools
Performance Optimization
Optimizing your IoT remote SSH server can significantly enhance its efficiency and reliability. Consider these optimization strategies:
Resource Management
- Enable compression for data transfer
- Implement connection multiplexing
- Optimize keep-alive settings
- Use persistent connections where appropriate
Advanced Configuration
- Implement load balancing for high-traffic environments
- Configure rate limiting to prevent abuse
- Use connection pooling for better resource utilization
- Implement automated session management
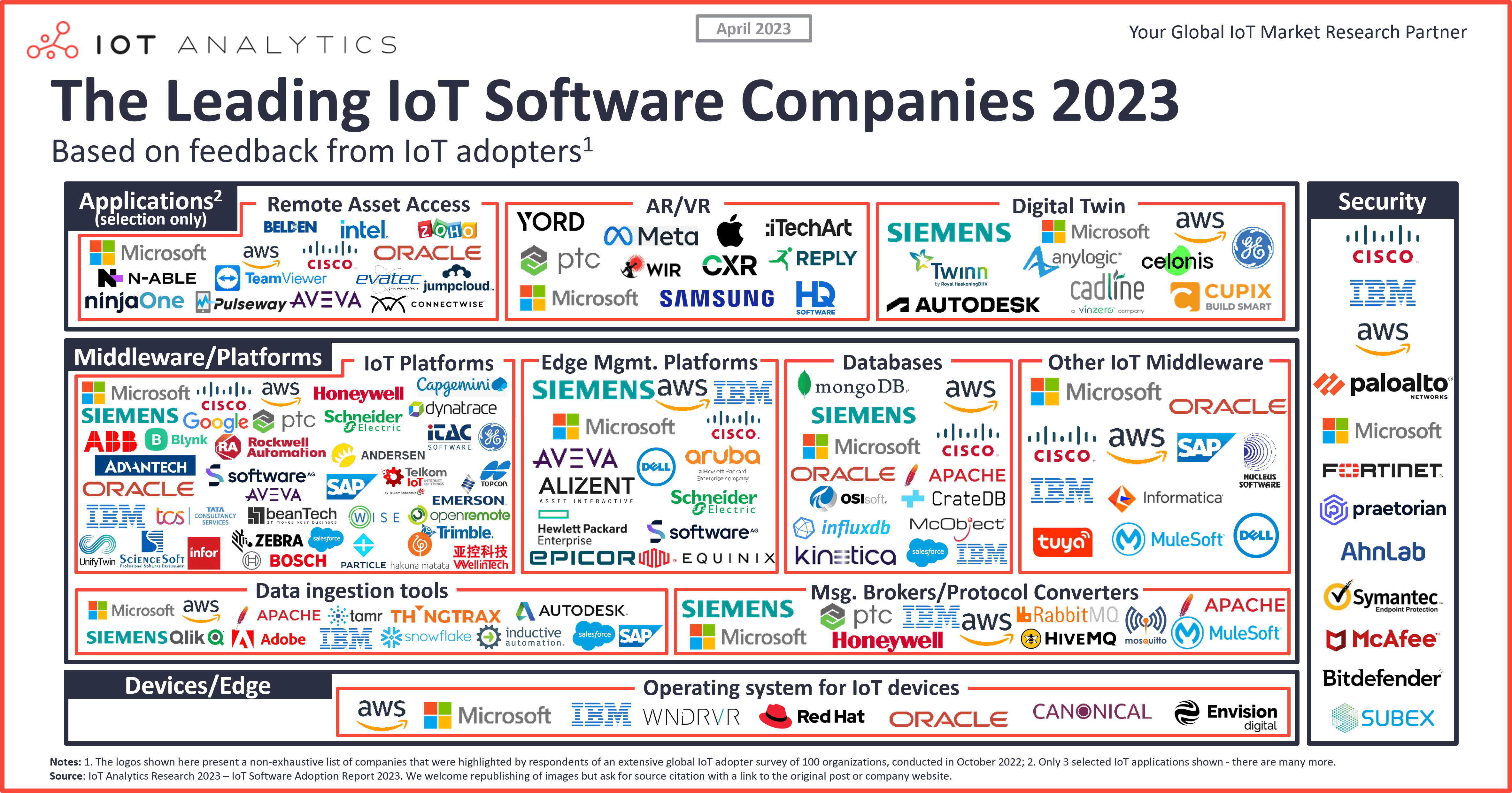
Research conducted by IoT Analytics shows that optimized SSH configurations can reduce connection times by up to 40% while maintaining security integrity. [Source: IoT Analytics Performance Study 2023]
Troubleshooting Tips
Even with careful implementation, issues may arise with your IoT remote SSH server. Here are common problems and their solutions:
Connection Issues
- Verify network connectivity and firewall settings
- Check SSH service status and logs
- Validate correct port configuration
- Ensure proper DNS resolution
Performance Problems
- Analyze server load and resource usage
- Check for network congestion
- Verify encryption algorithm efficiency
- Monitor connection timeouts
Future Trends in IoT Remote Access
The landscape of IoT remote access continues to evolve rapidly. Here are key trends shaping the future:
Emerging Technologies
- Quantum-resistant encryption protocols
- AI-powered access management systems
- Blockchain-based authentication methods
- Edge computing integration
Market Developments
- Increased adoption of zero-trust architecture
- Development of IoT-specific SSH standards
- Enhanced mobile device management integration
- Improved cross-platform compatibility
Comparison Chart of SSH Servers
| Feature | OpenSSH | Dropbear SSH | TinySSH |
|---|---|---|---|
| Memory Footprint | Medium | Small | Very Small |
| Security Features | Extensive | Basic | Minimal |
| Platform Support | Wide | Limited | Very Limited |
| Performance | Excellent | Good | Fair |
| Community Support | Strong | Moderate | Weak |
Technical Requirements
Before implementing your IoT remote SSH server, ensure your system meets these technical requirements:
Hardware Specifications
- Minimum 512MB RAM (1GB recommended)
- At least 1GHz processor
- 2GB storage space
- Network interface with stable internet connection
Software Requirements
- Linux-based operating system (preferred)
- Latest security patches installed
- Compatible SSH server software
- Monitoring tools installed
Conclusion
Implementing the best IoT remote SSH server solution is crucial for maintaining secure and efficient remote access to your IoT infrastructure. Throughout this guide, we've explored various SSH server options, security best practices, implementation strategies, and future trends in IoT remote access. By carefully selecting and configuring your SSH server, you can ensure both operational efficiency and robust security for your IoT devices.
We encourage you to share your experiences with IoT remote SSH server implementations in the comments section below. If you found this guide helpful, please consider sharing it with your network and exploring our other technical resources for more in-depth information on IoT security and management solutions.