Remote access to IoT devices through SSH has become a cornerstone of modern connectivity, enabling users to manage and control their devices from anywhere in the world. With the growing adoption of Internet of Things (IoT) technology, the ability to securely access these devices remotely is more important than ever. Whether you're managing smart home systems, industrial IoT applications, or network infrastructure, SSH (Secure Shell) offers a robust and encrypted way to interact with your devices. This article explores the best remote access IoT devices through SSH, providing you with actionable insights and practical solutions to optimize your IoT management strategies.
As IoT devices continue to proliferate across industries, ensuring their security and accessibility is critical. SSH is widely regarded as one of the most secure protocols for remote device management, offering encryption, authentication, and data integrity. However, not all IoT devices are created equal, and selecting the right tools and configurations for SSH access can be challenging. In this article, we will delve into the top IoT devices that support SSH, discuss their features, and provide step-by-step guidance for setting up secure remote access.
By the end of this article, you will have a comprehensive understanding of how to leverage SSH for remote IoT device management. We will also address key considerations such as security best practices, troubleshooting tips, and tools to enhance your SSH experience. Whether you're a tech enthusiast, IT professional, or IoT developer, this guide will equip you with the knowledge to make informed decisions and maximize the potential of your IoT ecosystem.
Read also:Movierulz 5 Kannada A Comprehensive Guide To Streaming Kannada Movies Online
Table of Contents
- Introduction to SSH and IoT
- Why SSH is Essential for Remote Access
- Top IoT Devices for SSH Remote Access
- Setting Up SSH on IoT Devices
- Security Best Practices for SSH
- Tools to Enhance SSH Experience
- Troubleshooting Common SSH Issues
- Case Studies: Successful SSH IoT Implementations
- Future Trends in SSH and IoT
- Conclusion
Introduction to SSH and IoT
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over unsecured networks. It is widely used for remote administration of devices, file transfers, and executing commands. In the context of IoT, SSH allows users to securely access and manage devices such as routers, smart home controllers, and industrial sensors. This section provides an overview of how SSH works and its relevance to IoT ecosystems.
SSH operates on a client-server model, where the client initiates a connection to the server. The protocol uses strong encryption algorithms to protect data in transit, ensuring confidentiality and integrity. Additionally, SSH supports public-key authentication, which enhances security by eliminating the need for password-based logins. These features make SSH an ideal choice for managing IoT devices, especially in environments where data security is paramount.
IoT devices, on the other hand, are interconnected devices that collect and exchange data over the internet. They range from consumer-grade products like smart thermostats and cameras to enterprise-level solutions such as industrial automation systems. Many IoT devices come with built-in SSH capabilities, allowing users to remotely configure settings, monitor performance, and troubleshoot issues. Understanding the synergy between SSH and IoT is the first step toward unlocking their full potential.
Why SSH is Essential for Remote Access
SSH is not just another remote access tool; it is a critical component of secure IoT management. Unlike other protocols, SSH provides end-to-end encryption, ensuring that sensitive data remains protected from eavesdropping and man-in-the-middle attacks. This section highlights the key reasons why SSH is indispensable for remote access to IoT devices.
First and foremost, SSH offers unparalleled security. By encrypting all data transmitted between the client and server, SSH prevents unauthorized access and data breaches. This is particularly important for IoT devices, which often handle sensitive information such as personal data, financial transactions, or industrial secrets. SSH's robust authentication mechanisms, including password-based and public-key authentication, further enhance its security posture.
Another advantage of SSH is its versatility. It supports a wide range of functionalities, from executing commands and transferring files to tunneling other protocols. This makes SSH a one-stop solution for managing IoT devices, eliminating the need for multiple tools. Additionally, SSH is platform-independent, meaning it can be used on various operating systems, including Linux, Windows, and macOS. This cross-platform compatibility ensures seamless integration with diverse IoT ecosystems.
Read also:Max Kannada Download Movierulz A Comprehensive Guide To Streaming Kannada Movies Online
Top IoT Devices for SSH Remote Access
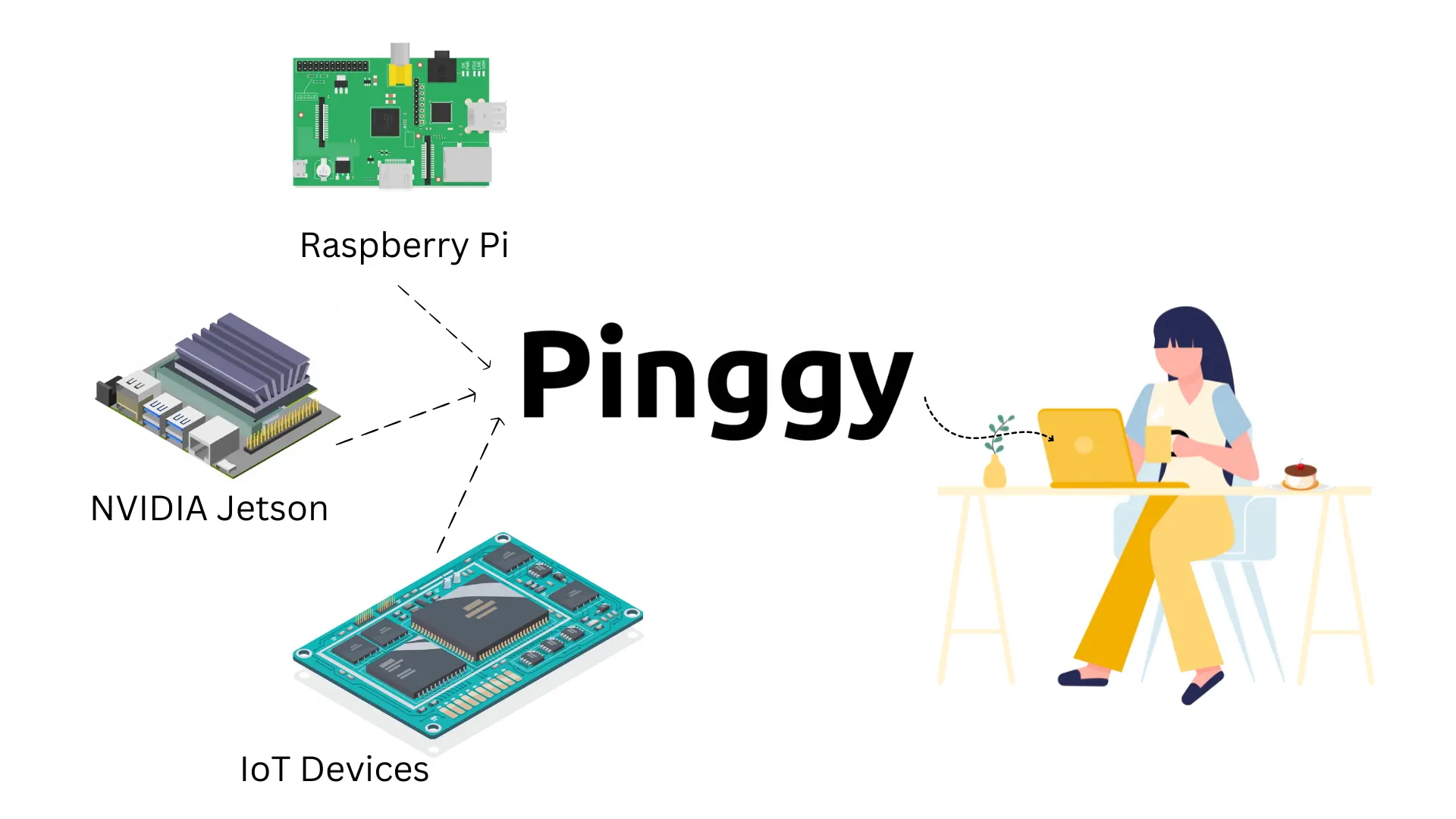
When it comes to remote access through SSH, not all IoT devices are created equal. Some devices are specifically designed with SSH capabilities in mind, offering advanced features and seamless integration. Below, we explore the top IoT devices that excel in SSH remote access, along with their key features and benefits.
Raspberry Pi
Raspberry Pi is a versatile single-board computer that has gained immense popularity among IoT enthusiasts. It supports SSH out of the box, making it an excellent choice for remote device management. With its low cost, compact size, and extensive community support, Raspberry Pi is ideal for a wide range of applications, from home automation to industrial IoT.
Key Features:
- Built-in SSH support
- Wide compatibility with sensors and peripherals
- Active community and extensive documentation
Ubiquiti UniFi
Ubiquiti UniFi is a line of networking products designed for enterprise and home use. Its devices, including routers and access points, support SSH for advanced configuration and monitoring. UniFi's intuitive interface and robust performance make it a top choice for managing IoT networks.
Key Features:
- Enterprise-grade security
- Centralized management platform
- High scalability for IoT deployments
Arduino
Arduino is a popular open-source platform for building IoT projects. While it does not natively support SSH, users can enable SSH by integrating it with compatible hardware such as Raspberry Pi or ESP32. Arduino's flexibility and ease of use make it a favorite among hobbyists and professionals alike.
Key Features:
- Extensive library support
- Customizable for various IoT applications
- Low power consumption
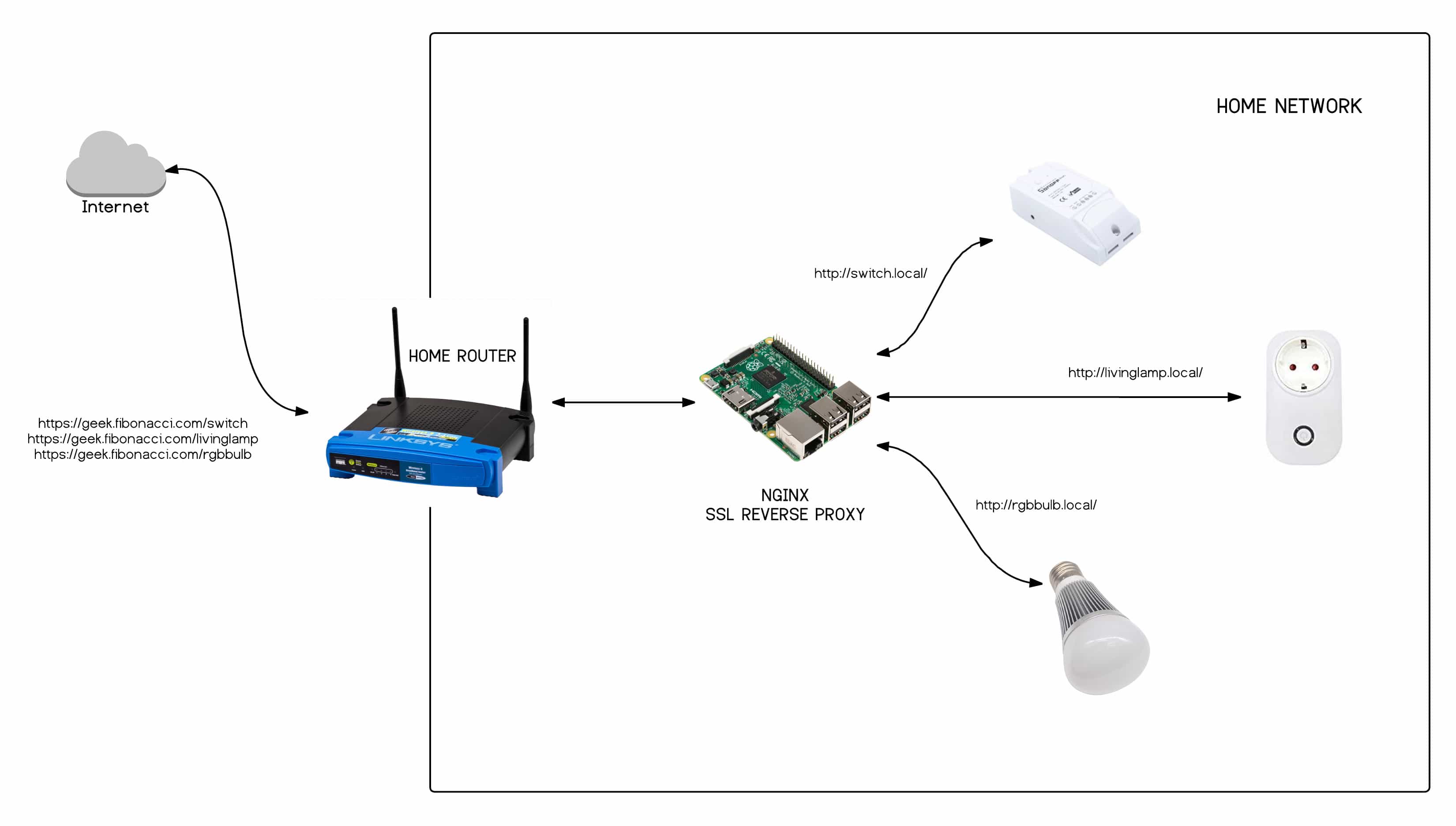
Setting Up SSH on IoT Devices
Setting up SSH on IoT devices is a straightforward process, but it requires careful attention to detail to ensure security and functionality. This section provides a step-by-step guide to configuring SSH on popular IoT devices, along with tips for optimizing performance.
For devices like Raspberry Pi, SSH can be enabled through the device's configuration menu or by creating a blank file named "ssh" in the boot directory. Once enabled, users can connect to the device using an SSH client such as PuTTY or OpenSSH. It is essential to change the default credentials and configure public-key authentication to enhance security.
For Ubiquiti UniFi devices, SSH access can be enabled through the UniFi Controller software. Users can then connect to the device using an SSH client and execute commands for advanced configuration. Similarly, Arduino users can enable SSH by integrating it with compatible hardware and configuring the necessary software libraries.
Security Best Practices for SSH
While SSH is inherently secure, improper configuration can expose IoT devices to vulnerabilities. This section outlines best practices for securing SSH connections and protecting IoT devices from cyber threats.
First, always use strong passwords or, preferably, public-key authentication. Public-key authentication eliminates the risk of brute-force attacks by requiring users to possess a private key for access. Additionally, disable password-based authentication and root login to further enhance security.
Another important practice is to change the default SSH port (22) to a non-standard port. This reduces the likelihood of automated attacks targeting the default port. Regularly updating firmware and software is also crucial to patch known vulnerabilities and ensure optimal performance.
Tools to Enhance SSH Experience
Several tools can enhance the SSH experience, making it more efficient and user-friendly. This section highlights some of the most popular tools and their features.
OpenSSH: A widely used open-source implementation of the SSH protocol, offering robust security and extensive functionality.
PuTTY: A lightweight SSH client for Windows, known for its simplicity and ease of use.
MobaXterm: An advanced SSH client that combines multiple tools, including a terminal, file transfer, and network utilities.
Troubleshooting Common SSH Issues
Despite its reliability, SSH can sometimes encounter issues that hinder connectivity. This section addresses common problems and provides solutions to resolve them.
One frequent issue is connection timeouts, which can occur due to network instability or incorrect firewall settings. To resolve this, ensure that the SSH port is open and accessible, and verify the network configuration. Another common problem is authentication failures, which can be addressed by double-checking credentials and ensuring that public-key authentication is properly configured.
Case Studies: Successful SSH IoT Implementations
This section presents real-world examples of organizations and individuals who have successfully implemented SSH for IoT device management. These case studies demonstrate the practical benefits of SSH and provide valuable insights for readers.
Future Trends in SSH and IoT
As IoT technology continues to evolve, so too will the tools and protocols used to manage it. This section explores emerging trends in SSH and IoT, including advancements in encryption, automation, and integration with cloud platforms.
Conclusion
In conclusion, SSH is an indispensable tool for remote access to IoT devices, offering unparalleled security and versatility. By selecting the right IoT devices, configuring SSH properly, and following best practices, users can unlock the full potential of their IoT ecosystems. We encourage you to share your thoughts and experiences in the comments below, and explore our other articles for more insights into IoT and remote access technologies.