In today's interconnected world, the Internet of Things (IoT) has become an integral part of our daily lives. From smart homes to industrial automation, IoT devices are transforming the way we interact with technology. However, managing these devices securely and efficiently can be a challenge. This is where AWS (Amazon Web Services) and SSH (Secure Shell) come into play. By leveraging AWS's robust cloud infrastructure and SSH's secure communication protocols, businesses and individuals can effectively manage their IoT devices while ensuring data security and operational efficiency.
As the number of IoT devices continues to grow exponentially, reaching over 14.4 billion active connections in 2023 according to IoT Analytics, the need for secure device management has never been more crucial. AWS provides a comprehensive suite of services specifically designed to handle IoT workloads, while SSH offers a secure channel for remote device management and data transfer.
This article will guide you through the essential aspects of managing IoT devices using AWS and SSH, covering everything from basic concepts to advanced implementation strategies. Whether you're a system administrator, IoT developer, or cloud architect, this comprehensive guide will provide you with the knowledge and tools necessary to implement secure IoT solutions in the AWS cloud environment.
Read also:Exploring Eden Fantasies A Journey Into Paradise
Table of Contents
- Understanding IoT and Its Significance
- AWS IoT Overview and Core Services
- Implementing Secure Communication with SSH
- AWS IoT Security Features and Best Practices
- Efficient IoT Device Management on AWS
- Data Processing and Analytics for IoT
- Scaling IoT Solutions with AWS
- Troubleshooting and Monitoring IoT Systems
- Cost Optimization Strategies for IoT on AWS
- Future Trends in IoT and Cloud Computing
Understanding IoT and Its Significance
The Internet of Things (IoT) represents a network of physical objects embedded with sensors, software, and connectivity capabilities that enable them to collect and exchange data. These objects, or "things," can range from simple household devices like smart thermostats to complex industrial machinery. The global IoT market is projected to reach $1.1 trillion by 2026, according to MarketsandMarkets research.
IoT technology offers numerous benefits across various industries:
- Enhanced operational efficiency through real-time monitoring
- Improved decision-making based on data analytics
- Cost savings through predictive maintenance
- Increased safety and security in industrial environments
Key Components of IoT Systems
Understanding the fundamental components of IoT systems is crucial for effective implementation:
- Sensors and Actuators: Collect environmental data and trigger actions
- Connectivity: Wireless protocols like Wi-Fi, Bluetooth, and cellular networks
- Data Processing: Edge computing and cloud-based analytics
- User Interface: Mobile applications and web dashboards
AWS IoT Overview and Core Services
AWS provides a comprehensive set of services specifically designed for IoT applications. The AWS IoT platform enables secure, bi-directional communication between internet-connected devices and the AWS cloud. According to AWS documentation, their IoT services can support billions of devices and trillions of messages.
Core AWS IoT Services
- AWS IoT Core: Enables secure device connectivity and message routing
- AWS IoT Greengrass: Extends AWS to edge devices
- AWS IoT Analytics: Collects and analyzes IoT data
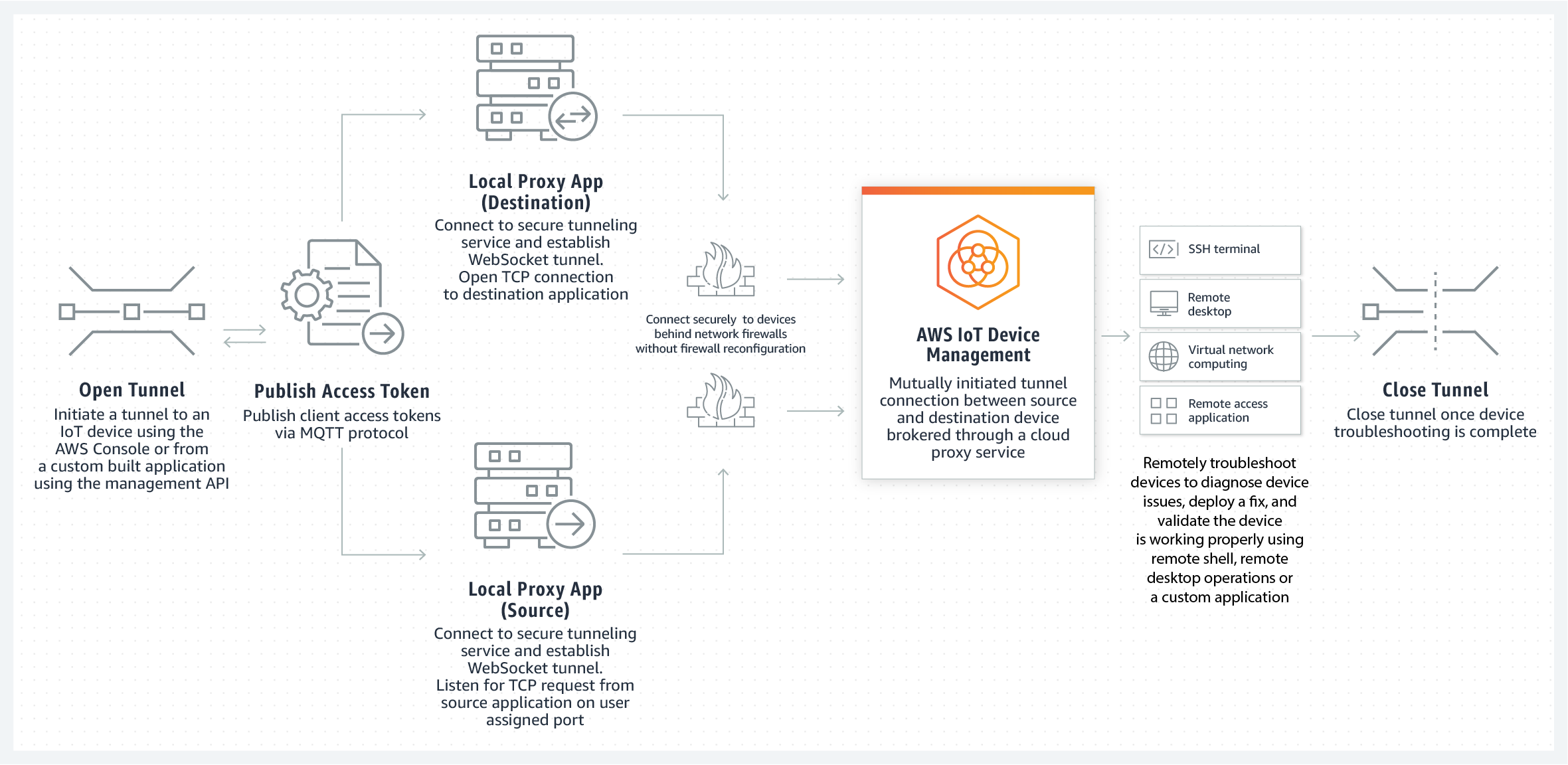
- AWS IoT Device Management: Simplifies device onboarding and organization
These services work together to provide a complete solution for building, deploying, and managing IoT applications at scale. The platform's scalability and reliability make it suitable for both small-scale projects and enterprise-level implementations.
Implementing Secure Communication with SSH
Secure Shell (SSH) plays a vital role in managing IoT devices securely. SSH provides encrypted communication channels between devices and servers, ensuring data confidentiality and integrity. According to the SSH Communications Security report, over 90% of enterprises use SSH for secure remote access.
Read also:Bongocam The Ultimate Guide To Enhancing Your Social Connections
Best Practices for SSH Implementation
- Use strong, unique passwords and key pairs
- Implement multi-factor authentication
- Regularly update SSH software and configurations
- Restrict access using IP whitelisting
- Monitor and log SSH sessions
When combined with AWS IoT services, SSH creates a robust security framework that protects both device communications and management operations.
AWS IoT Security Features and Best Practices
AWS IoT incorporates multiple layers of security to protect devices and data. The platform uses X.509 certificates for device authentication and implements end-to-end encryption using TLS 1.2. According to AWS security documentation, their IoT services undergo regular third-party audits and penetration testing.
Security Implementation Steps
- Register and authenticate devices using unique certificates
- Implement device policies and access controls
- Use AWS IoT Device Defender for continuous monitoring
- Enable AWS WAF for web application protection
- Implement data encryption at rest and in transit
These security measures, when properly implemented, create a comprehensive protection framework that meets industry standards and regulatory requirements.
Efficient IoT Device Management on AWS
Managing large-scale IoT deployments requires sophisticated tools and strategies. AWS IoT Device Management provides features for organizing, monitoring, and maintaining device fleets efficiently. According to AWS case studies, some customers have successfully managed millions of devices using these services.
Device Management Features
- Device grouping and tagging
- Remote software updates
- Device state monitoring
- Automated provisioning
- Custom metrics and reporting
The platform's API-driven architecture allows for seamless integration with existing enterprise systems and custom applications.
Data Processing and Analytics for IoT
Effective data processing is crucial for deriving value from IoT implementations. AWS offers a complete ecosystem for collecting, processing, and analyzing IoT data. According to IDC research, organizations that effectively analyze IoT data can achieve up to 25% improvement in operational efficiency.
Data Processing Workflow
- Data ingestion using AWS IoT Core
- Real-time processing with AWS Lambda
- Storage in Amazon S3 or DynamoDB
- Analysis using AWS IoT Analytics
- Visualization with Amazon QuickSight
This comprehensive data processing pipeline enables organizations to transform raw sensor data into actionable insights.
Scaling IoT Solutions with AWS
As IoT deployments grow, scaling becomes a critical consideration. AWS provides several mechanisms for scaling IoT solutions efficiently. The platform's serverless architecture and auto-scaling capabilities ensure that resources can adapt to changing demands automatically.
Scaling Strategies
- Horizontal scaling through AWS IoT Rules Engine
- Vertical scaling using AWS Lambda functions
- Edge scaling with AWS IoT Greengrass
- Database scaling using Amazon DynamoDB
- Network scaling through AWS Global Accelerator
These scaling mechanisms help organizations handle increasing device numbers and data volumes without compromising performance.
Troubleshooting and Monitoring IoT Systems
Effective troubleshooting and monitoring are essential for maintaining IoT system reliability. AWS provides comprehensive tools for monitoring and diagnosing issues in IoT deployments. According to AWS operational metrics, their monitoring services can reduce mean time to resolution (MTTR) by up to 70%.
Monitoring Tools and Techniques
- AWS CloudWatch for performance monitoring
- AWS IoT Device Defender for security monitoring
- Amazon CloudTrail for API logging
- AWS X-Ray for distributed tracing
- Custom dashboards using Amazon QuickSight
These tools, when used effectively, provide complete visibility into IoT system operations and help prevent potential issues before they impact users.
Cost Optimization Strategies for IoT on AWS
Managing costs is crucial for successful IoT implementations. AWS offers various pricing models and cost optimization tools to help organizations control their IoT expenses. According to AWS cost management documentation, customers can achieve up to 30% cost savings through proper optimization strategies.
Cost Optimization Techniques
- Use reserved instances for predictable workloads
- Implement spot instances for non-critical tasks
- Optimize data storage using lifecycle policies
- Use AWS Cost Explorer for cost analysis
- Implement automated scaling policies
These strategies help organizations maximize their return on investment while maintaining system performance and reliability.
Future Trends in IoT and Cloud Computing
The IoT landscape continues to evolve rapidly, with several key trends shaping its future development. According to Gartner research, edge computing and AI integration are expected to be major growth areas in IoT technology.
Emerging Trends to Watch
- Increased adoption of edge computing
- Integration with artificial intelligence
- Expansion of 5G networks
- Growth of digital twins technology
- Development of new IoT standards
These trends indicate a future where IoT systems become more intelligent, responsive, and integrated with other emerging technologies.
Conclusion
Managing IoT devices securely and efficiently in the AWS cloud environment requires a comprehensive approach that combines robust security measures, effective device management, and optimized data processing. By leveraging AWS IoT services and implementing secure communication protocols like SSH, organizations can build scalable, reliable IoT solutions that meet modern business requirements.
We encourage you to explore these concepts further and consider how they might apply to your specific use case. If you have any questions or experiences to share about managing IoT devices on AWS, please leave a comment below. Additionally, check out our other articles for more in-depth technical guides and best practices in cloud computing and IoT implementation.