In today's interconnected world, the Internet of Things (IoT) has revolutionized how devices communicate and share data. However, ensuring secure communication between IoT devices and cloud platforms like AWS is crucial. One of the most effective ways to achieve this is through SSH tunneling. This article delves into the concept of IoT SSH tunnel AWS, explaining how it works, its benefits, and how you can implement it to enhance your IoT infrastructure's security.
As businesses increasingly rely on IoT devices for data collection and automation, the need for robust security measures becomes paramount. IoT devices often operate in remote or unsecured environments, making them vulnerable to cyber threats. By leveraging AWS and SSH tunneling, organizations can create secure communication channels that protect sensitive data and ensure uninterrupted operations.
This article will guide you through the process of setting up an IoT SSH tunnel on AWS, providing step-by-step instructions and expert insights. Whether you're a seasoned IT professional or new to IoT and cloud computing, this guide will equip you with the knowledge and tools to implement secure remote access solutions effectively.
Read also:Is Lee Jong Suk Married Everything You Need To Know About His Relationship Status
Table of Contents
- Introduction to IoT and AWS
- What is SSH Tunneling?
- Benefits of IoT SSH Tunnel AWS
- Setting Up SSH Tunnel on AWS
- Best Practices for Secure IoT SSH Tunnel
- Common Challenges and Solutions
- Real-World Use Cases
- Advanced Features and Integrations
- Future of IoT and Cloud Security
- Conclusion
Introduction to IoT and AWS
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that enables them to collect and exchange data. AWS, Amazon's cloud platform, provides a robust infrastructure for managing and analyzing IoT data. Together, IoT and AWS create a powerful ecosystem for businesses to leverage real-time data insights and automation.
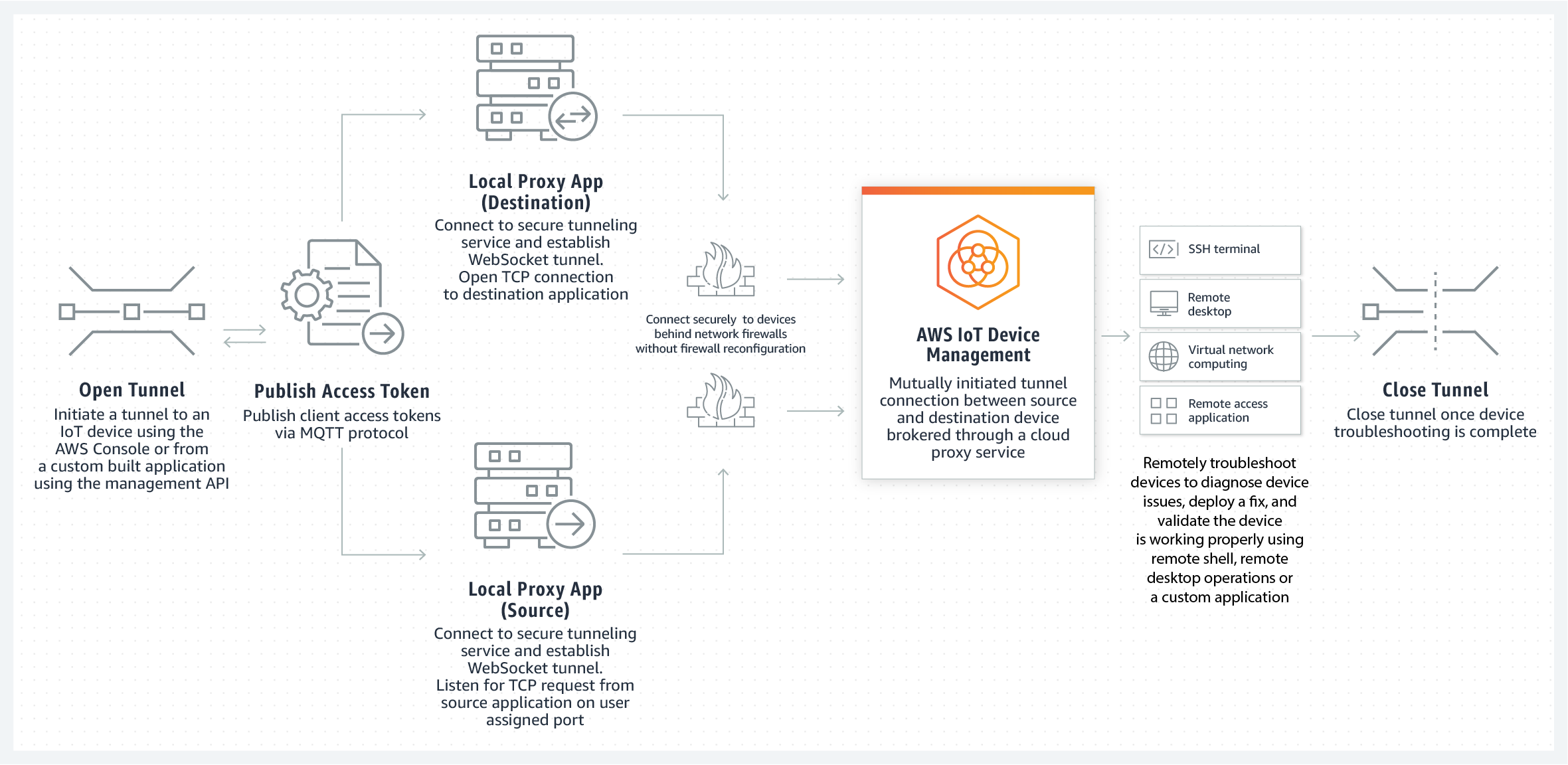
IoT devices generate massive amounts of data, which can be processed and analyzed on AWS to derive actionable insights. AWS offers specialized services like AWS IoT Core, which facilitates secure communication between devices and the cloud. By integrating IoT with AWS, organizations can scale their operations, improve efficiency, and enhance decision-making processes.
However, the integration of IoT with cloud platforms like AWS also introduces security challenges. Ensuring secure data transmission between IoT devices and AWS is essential to protect sensitive information and maintain system integrity.
What is SSH Tunneling?
SSH tunneling, also known as SSH port forwarding, is a method of creating a secure connection between a local device and a remote server. It works by encrypting data transmitted through the tunnel, preventing unauthorized access and eavesdropping. SSH tunneling is widely used to secure remote access to servers and devices.
There are three types of SSH tunneling:
- Local Port Forwarding: Redirects traffic from a local port to a remote server.
- Remote Port Forwarding: Redirects traffic from a remote server to a local port.
- Dynamic Port Forwarding: Creates a SOCKS proxy for routing traffic dynamically.
SSH tunneling is particularly useful for IoT devices that operate in unsecured environments. By establishing an SSH tunnel, organizations can ensure that data transmitted between IoT devices and AWS remains encrypted and secure.
Read also:Kent Benson Net Worth A Comprehensive Look At The Nba Legends Wealth And Achievements
Benefits of IoT SSH Tunnel AWS
Implementing an IoT SSH tunnel on AWS offers several advantages:
- Enhanced Security: SSH tunneling encrypts data, protecting it from interception and unauthorized access.
- Remote Access: Enables secure remote management of IoT devices from anywhere in the world.
- Scalability: AWS's infrastructure supports the seamless integration of IoT devices, ensuring scalability as your network grows.
- Cost Efficiency: Reduces the need for additional hardware or complex network configurations.
By leveraging AWS's robust cloud services and SSH tunneling, organizations can create a secure and scalable IoT infrastructure that meets their operational needs.
Setting Up SSH Tunnel on AWS
Setting up an SSH tunnel on AWS involves several steps:
Step 1: Launch an EC2 Instance
Create an EC2 instance on AWS, which will serve as the remote server for SSH tunneling. Ensure that the instance has the necessary permissions and security groups configured.
Step 2: Install SSH Server
Install an SSH server on the EC2 instance. For Linux-based instances, OpenSSH is commonly used. Verify that the SSH service is running and accessible.
Step 3: Configure Security Groups
Update the security group settings to allow SSH traffic (port 22) from your local machine or network. Restrict access to specific IP addresses for added security.
Step 4: Establish SSH Tunnel
Use an SSH client to establish a tunnel between your local machine and the EC2 instance. The command typically looks like this:
ssh -L [local_port]:[remote_host]:[remote_port] [user]@[ec2_instance_ip]
Step 5: Test the Tunnel
Verify that the SSH tunnel is working by accessing the remote service through the local port. Ensure that data transmission is encrypted and secure.
Best Practices for Secure IoT SSH Tunnel
To ensure the security of your IoT SSH tunnel on AWS, follow these best practices:
- Use Strong Authentication: Implement multi-factor authentication (MFA) for SSH access.
- Limit Access: Restrict SSH access to specific IP addresses or networks.
- Regularly Update Software: Keep your SSH server and client software up to date with the latest security patches.
- Monitor Logs: Regularly review SSH logs for suspicious activity or unauthorized access attempts.
By adhering to these practices, you can minimize security risks and ensure the integrity of your IoT infrastructure.
Common Challenges and Solutions
Implementing an IoT SSH tunnel on AWS can present several challenges:
Challenge 1: Network Latency
High network latency can affect the performance of SSH tunnels. To mitigate this, optimize your network configuration and use AWS regions closest to your IoT devices.
Challenge 2: Device Compatibility
Not all IoT devices support SSH tunneling. In such cases, consider using a gateway device that can establish the SSH tunnel on behalf of the IoT devices.
Challenge 3: Scalability
As the number of IoT devices grows, managing SSH tunnels can become complex. Use automation tools and scripts to streamline the process and ensure scalability.
Real-World Use Cases
IoT SSH tunnel AWS is used in various industries to enhance security and efficiency:
Use Case 1: Smart Home Automation
Securely manage and control smart home devices remotely using SSH tunnels on AWS.
Use Case 2: Industrial IoT
Enable secure communication between industrial sensors and AWS for real-time monitoring and analysis.
Use Case 3: Healthcare IoT
Protect sensitive patient data transmitted from medical IoT devices to AWS using SSH tunneling.
Advanced Features and Integrations
AWS offers several advanced features that can enhance IoT SSH tunneling:
- AWS Lambda: Automate tasks and processes triggered by IoT data.
- AWS IoT Greengrass: Extend AWS capabilities to edge devices for local processing.
- AWS CloudWatch: Monitor and analyze IoT data in real-time.
Integrating these features with SSH tunneling can further enhance the security and functionality of your IoT infrastructure.
Future of IoT and Cloud Security
As IoT and cloud technologies continue to evolve, the importance of secure communication will only increase. Innovations in encryption, authentication, and network protocols will play a crucial role in shaping the future of IoT and cloud security.
Organizations must stay informed about emerging trends and technologies to ensure their IoT infrastructures remain secure and resilient against evolving cyber threats.
Conclusion
IoT SSH tunnel AWS provides a secure and scalable solution for managing IoT devices and data. By leveraging SSH tunneling and AWS's robust cloud services, organizations can protect sensitive information, ensure uninterrupted operations, and enhance decision-making processes.
We encourage you to implement the strategies and best practices discussed in this article to secure your IoT infrastructure. If you have any questions or insights, feel free to leave a comment below. For more information, explore our other articles on IoT and cloud security.