Are you looking for ways to access your IoT devices securely and efficiently without spending a dime? SSH (Secure Shell) access is one of the most reliable methods to manage and interact with your IoT devices remotely. In this article, we will explore how you can gain SSH access to your IoT devices for free, ensuring both security and ease of use. With the growing popularity of IoT (Internet of Things) devices, the need for secure remote access has become more critical than ever. Whether you are a hobbyist, a developer, or a tech enthusiast, understanding how to configure and use SSH for your IoT devices can significantly enhance your ability to manage them effectively.
IoT devices, ranging from smart home gadgets to industrial sensors, often require remote management to ensure they function optimally. SSH provides a secure channel over an unsecured network, allowing you to execute commands, transfer files, and manage configurations without exposing your devices to potential threats. This article will guide you through the steps to set up SSH access for free, ensuring that your IoT devices remain secure and accessible.
In the following sections, we will delve into the details of SSH, its importance in IoT device management, and the step-by-step process to configure SSH access without incurring any costs. By the end of this guide, you will have a comprehensive understanding of how to leverage SSH for your IoT devices, empowering you to manage them with confidence and efficiency.
Read also:Amaury Guichons Girlfriend A Glimpse Into The Life Of The Renowned Pastry Chef
Table of Contents
- What is SSH and Why is it Important?
- Benefits of Using SSH for IoT Devices
- Free Tools and Platforms for SSH Access
- Step-by-Step Guide to Setting Up SSH Access
- Troubleshooting Common SSH Issues
- Security Tips for SSH Access
- Advanced Features of SSH for IoT Devices
- Real-World Use Cases of SSH in IoT
- Conclusion and Call to Action
What is SSH and Why is it Important?
SSH, or Secure Shell, is a cryptographic network protocol used to secure data communication between two computers over an unsecured network. It provides a secure channel for executing commands, transferring files, and managing network services. SSH is widely used in IoT device management due to its ability to encrypt data and authenticate users, ensuring that sensitive information remains protected from unauthorized access.
The importance of SSH in IoT device management cannot be overstated. IoT devices often operate in environments where security is a top priority, such as smart homes, industrial automation, and healthcare systems. SSH ensures that remote access to these devices is secure, preventing potential cyberattacks and unauthorized access. By using SSH, you can confidently manage your IoT devices without compromising their security.
Benefits of Using SSH for IoT Devices
There are several benefits to using SSH for managing IoT devices:
- Security: SSH encrypts all data transmitted between the client and the server, protecting it from eavesdropping and man-in-the-middle attacks.
- Authentication: SSH uses public-key cryptography to authenticate users, ensuring that only authorized individuals can access the device.
- Efficiency: SSH allows you to execute commands and transfer files quickly and efficiently, making it ideal for managing multiple IoT devices simultaneously.
- Flexibility: SSH supports a wide range of applications, including remote shell access, file transfer, and tunneling, making it a versatile tool for IoT device management.
Free Tools and Platforms for SSH Access
Fortunately, there are several free tools and platforms available that allow you to access your IoT devices via SSH without any cost. Some of the most popular options include:
- OpenSSH: A widely used open-source implementation of the SSH protocol, available for Linux, macOS, and Windows.
- PuTTY: A free SSH client for Windows that provides a user-friendly interface for managing SSH connections.
- Termius: A cross-platform SSH client that offers a free tier with basic features for managing IoT devices.
- MobaXterm: A comprehensive tool for remote computing that includes SSH capabilities and is available for free.
Step-by-Step Guide to Setting Up SSH Access
Prerequisites for SSH Configuration
Before you begin configuring SSH access for your IoT device, ensure that you have the following:
- A computer or device with an SSH client installed.
- Network connectivity between your computer and the IoT device.
- Administrative access to the IoT device to configure SSH settings.
Configuring SSH on Your IoT Device
Follow these steps to configure SSH access on your IoT device:
Read also:Darren Naugles The Inspiring Journey Of A Baseball Legend
- Access the IoT device's settings or configuration interface.
- Enable the SSH service and configure the necessary settings, such as port number and authentication method.
- Generate SSH keys if required and store them securely.
- Test the SSH connection from your computer to ensure it is working correctly.
Troubleshooting Common SSH Issues
While configuring SSH access, you may encounter some common issues. Here are a few troubleshooting tips:
- Connection Refused: Ensure that the SSH service is running on the IoT device and that the correct port is open.
- Authentication Failed: Verify that the SSH keys or credentials are correct and match those configured on the device.
- Slow Performance: Check the network connection and ensure that there is no excessive latency or packet loss.
Security Tips for SSH Access
To ensure the security of your SSH connections, follow these best practices:
- Use strong, unique passwords or SSH keys for authentication.
- Disable password-based authentication and rely solely on SSH keys.
- Regularly update the SSH software on both the client and server sides to patch any vulnerabilities.
- Limit SSH access to specific IP addresses or networks to reduce the risk of unauthorized access.
Advanced Features of SSH for IoT Devices
SSH offers several advanced features that can enhance your IoT device management capabilities:
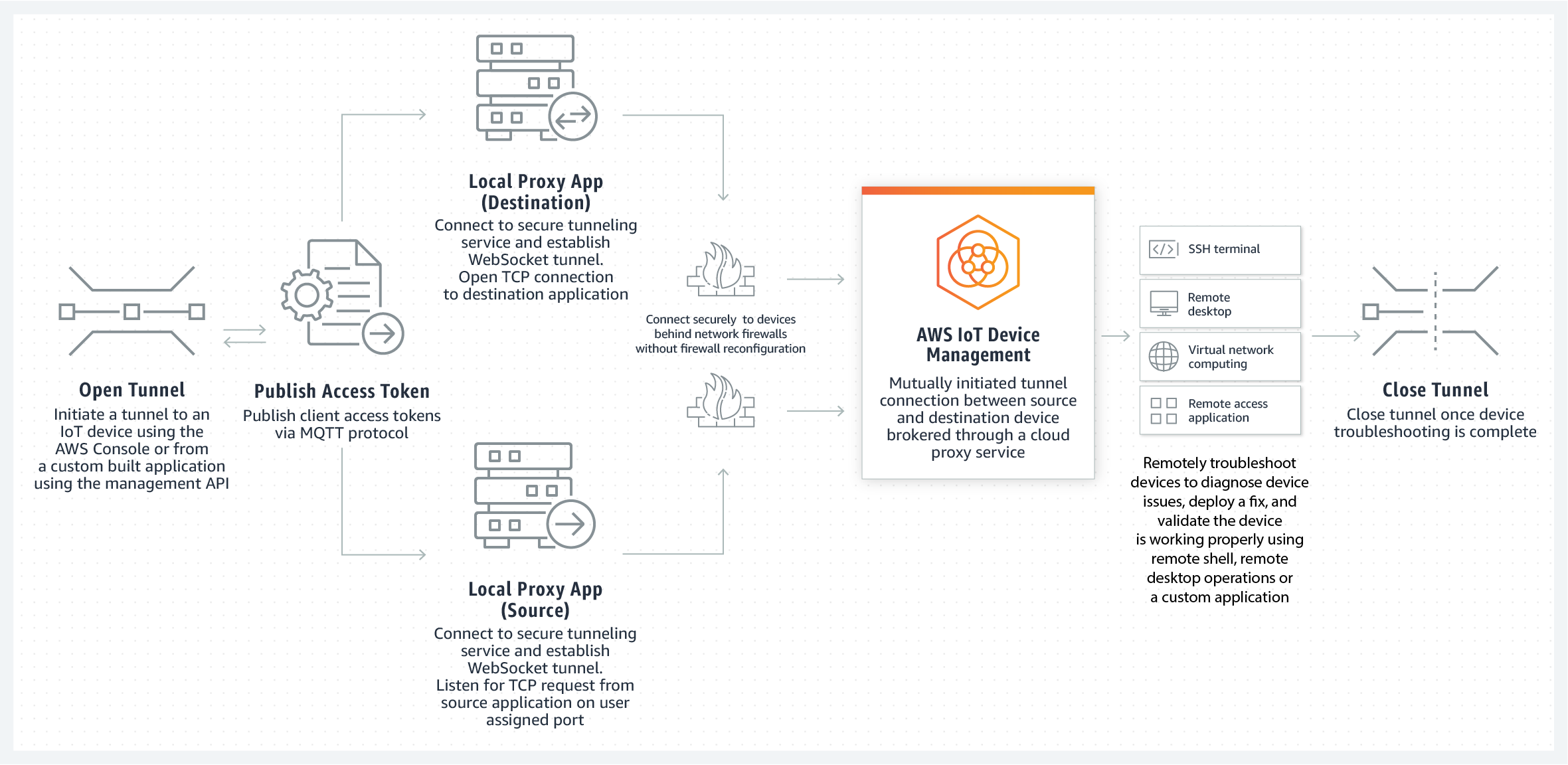
- Port Forwarding: Redirect network traffic through an SSH tunnel to access services securely.
- File Transfer: Use SCP (Secure Copy Protocol) or SFTP (SSH File Transfer Protocol) to transfer files securely.
- Automated Scripts: Execute automated scripts via SSH to streamline repetitive tasks.
Real-World Use Cases of SSH in IoT
SSH is widely used in various real-world applications for managing IoT devices. Some examples include:
- Smart Home Automation: SSH allows homeowners to remotely manage smart devices, such as thermostats and security cameras, ensuring they function optimally.
- Industrial IoT: SSH is used to monitor and control industrial equipment, enabling predictive maintenance and reducing downtime.
- Healthcare Systems: SSH ensures secure access to medical devices, protecting sensitive patient data and ensuring compliance with regulations.
Conclusion and Call to Action
In conclusion, SSH access is an essential tool for managing IoT devices securely and efficiently. By following the steps outlined in this guide, you can configure SSH access for free and ensure that your IoT devices remain protected from potential threats. Whether you are a hobbyist or a professional, leveraging SSH for your IoT devices can significantly enhance your ability to manage them effectively.
We encourage you to share your experiences with SSH access in the comments below and let us know if you have any questions or need further assistance. Additionally, feel free to explore our other articles for more insights into IoT device management and security. Together, let's make the world of IoT safer and more accessible for everyone!