In today's interconnected world, the Internet of Things (IoT) has become an integral part of our daily lives, revolutionizing how we interact with technology. SSH IoT AWS represents a crucial combination of technologies that ensures secure communication and management of IoT devices through Amazon Web Services (AWS). As more organizations embrace IoT solutions, understanding how to implement secure connections using SSH in AWS environments becomes essential for maintaining data integrity and system security. This article delves into the fundamental aspects of SSH IoT AWS, exploring its implementation, benefits, and best practices for securing your IoT infrastructure.
The integration of SSH with AWS IoT services offers a robust framework for managing remote devices while maintaining top-notch security standards. With millions of IoT devices connecting to cloud platforms daily, the need for secure authentication and data transmission has never been more critical. This comprehensive guide will walk you through the technical aspects of SSH IoT AWS, providing valuable insights for developers, system administrators, and IT professionals.
As we progress through this article, we'll examine the technical requirements, implementation steps, and security considerations necessary for successful SSH IoT AWS deployment. Whether you're new to IoT development or an experienced AWS practitioner, this resource will equip you with the knowledge to enhance your IoT security posture while leveraging the power of Amazon Web Services.
Read also:Max Movie Kannada Movierulz A Comprehensive Guide To Streaming Kannada Cinema
Table of Contents
- Understanding SSH IoT AWS
- Technical Requirements for SSH IoT AWS Implementation
- Step-by-Step Guide to Setting Up SSH IoT AWS
- Security Best Practices for SSH IoT AWS
- Advanced Configuration Options
- Troubleshooting Common SSH IoT AWS Issues
- Performance Optimization Techniques
- Cost Management and Resource Optimization
- Future Developments in SSH IoT AWS
- Conclusion and Next Steps
Understanding SSH IoT AWS
SSH IoT AWS represents a powerful combination of technologies that enables secure remote access and management of Internet of Things devices within Amazon Web Services infrastructure. Secure Shell (SSH) protocol serves as the foundation for encrypted communication between IoT devices and AWS cloud services, ensuring data integrity and confidentiality throughout the connection process.
The integration of SSH with AWS IoT Core provides several key benefits:
- End-to-end encryption for device communication
- Secure remote access to IoT devices
- Streamlined device management through AWS infrastructure
- Compliance with industry security standards
- Scalable architecture for growing IoT deployments
When implementing SSH IoT AWS, organizations can leverage various AWS services to enhance their IoT security posture:
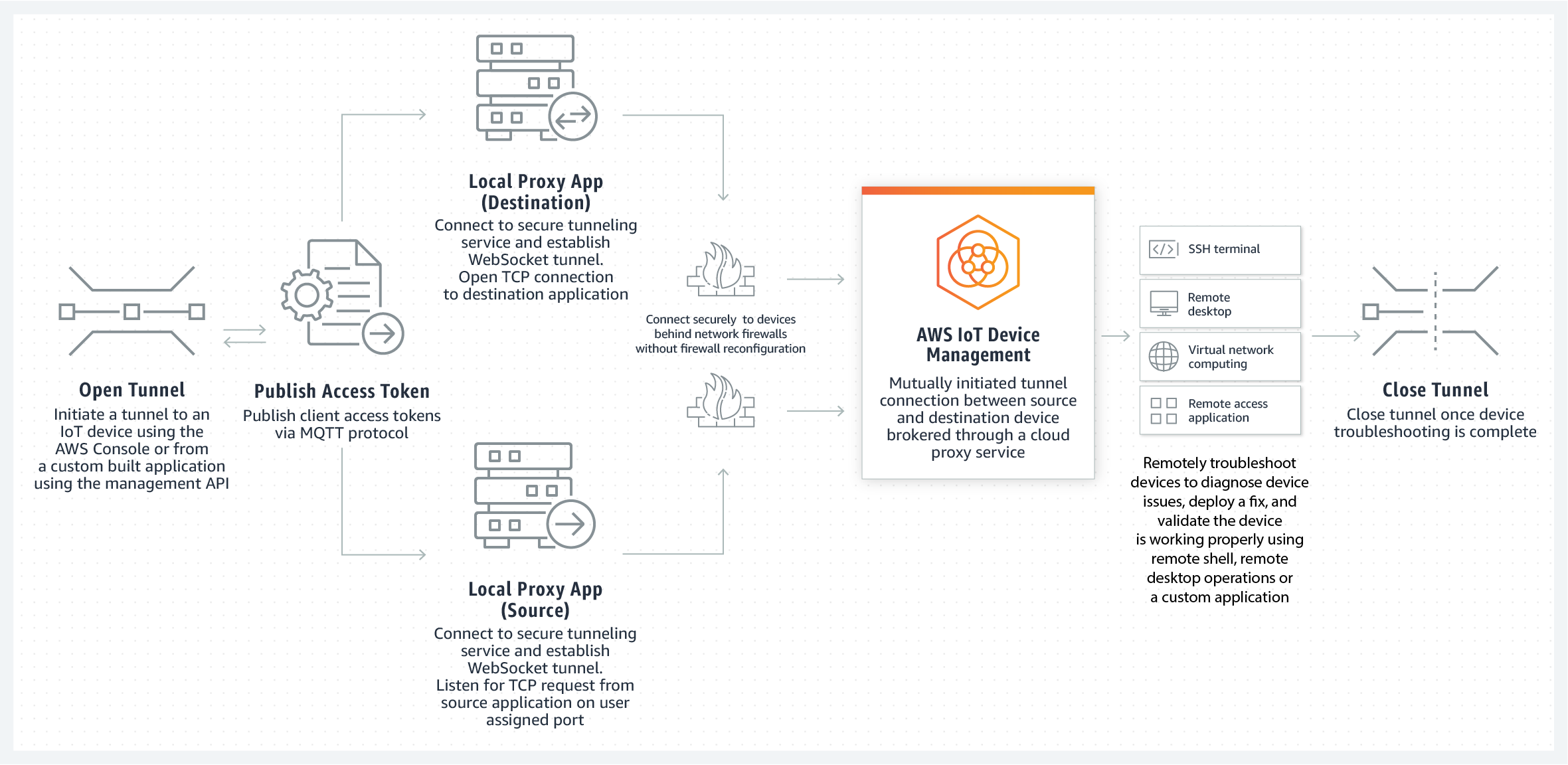
- AWS IoT Core for device management
- Amazon EC2 instances for secure gateways
- AWS Identity and Access Management (IAM) for access control
- AWS Key Management Service (KMS) for encryption key management
- Amazon CloudWatch for monitoring and logging
Technical Requirements for SSH IoT AWS Implementation
Successful deployment of SSH IoT AWS requires careful planning and preparation of technical components. The following requirements must be addressed before implementation:
SSH Key Management in AWS IoT
Proper SSH key management forms the backbone of secure IoT device communication. AWS provides robust mechanisms for generating, storing, and managing SSH keys:
- Generate RSA or ECDSA key pairs using AWS CLI or SDK
- Store private keys securely in AWS Systems Manager Parameter Store
- Automate key rotation using AWS Lambda functions
- Implement role-based access control for key access
Access Control and Permission Management
Implementing granular access control ensures only authorized users and devices can establish SSH connections:
Read also:Michelle Rodriguez Husband 2024 Everything You Need To Know
- Create IAM roles and policies for SSH access
- Configure AWS IoT policies for device authorization
- Implement multi-factor authentication (MFA)
- Set up IP whitelisting and network restrictions
Step-by-Step Guide to Setting Up SSH IoT AWS
This section provides a detailed walkthrough for implementing SSH IoT AWS:
- Prepare AWS Environment:
- Create necessary IAM roles and policies
- Set up AWS IoT Core registry
- Configure VPC and security groups
- Generate SSH Keys:
- Use AWS CLI to create key pairs
- Store private keys securely
- Register public keys in AWS IoT Core
- Configure IoT Devices:
- Install SSH client software
- Set up device certificates
- Configure device policies
- Establish Secure Connections:
- Test SSH connectivity
- Verify encryption protocols
- Monitor connection logs
Security Best Practices for SSH IoT AWS
Implementing robust security measures is crucial for protecting SSH IoT AWS deployments:
- Regularly rotate SSH keys and certificates
- Enable detailed logging and monitoring
- Implement network segmentation
- Use bastion hosts for secure access
- Conduct regular security audits
According to AWS security guidelines, organizations should:
- Maintain least privilege access principles
- Implement automated security checks
- Use AWS Shield for DDoS protection
- Enable AWS WAF for additional security layers
Advanced Configuration Options
For organizations requiring enhanced functionality, SSH IoT AWS offers several advanced configuration options:
- Custom authentication mechanisms
- Automated device provisioning
- Custom monitoring dashboards
- Integration with third-party security tools
Troubleshooting Common SSH IoT AWS Issues
When working with SSH IoT AWS, administrators may encounter various challenges:
- Connection timeouts
- Authentication failures
- Permission errors
- Network configuration issues
To address these issues:
- Verify security group settings
- Check IAM policies and permissions
- Review device registration status
- Examine CloudWatch logs for details
Performance Optimization Techniques
Optimizing SSH IoT AWS performance involves several strategies:
- Implement connection pooling
- Use keep-alive mechanisms
- Optimize encryption algorithms
- Enable compression for large data transfers
Cost Management and Resource Optimization
Effective cost management ensures efficient use of AWS resources:
- Monitor usage with AWS Cost Explorer
- Implement auto-scaling policies
- Use reserved instances for predictable workloads
- Optimize data transfer costs
Future Developments in SSH IoT AWS
The SSH IoT AWS ecosystem continues to evolve with new features and capabilities:
- Enhanced quantum-resistant encryption
- Improved device management tools
- Advanced monitoring and analytics
- Integrated AI-based security features
Conclusion and Next Steps
Implementing SSH IoT AWS provides organizations with a secure and scalable solution for managing IoT devices in cloud environments. By following the guidelines and best practices outlined in this article, businesses can establish robust connections while maintaining high security standards.
We encourage readers to:
- Explore AWS documentation for detailed implementation guides
- Participate in AWS community forums for support
- Share their experiences and insights in the comments section
- Consider implementing SSH IoT AWS in their own environments
For further reading, we recommend exploring additional resources:
- AWS IoT Core documentation
- Official AWS Security Best Practices
- SSH protocol specifications
- Industry case studies on IoT security