Managing IoT devices securely and efficiently is crucial in today's interconnected world. Secure Shell (SSH) plays a vital role in IoT device management, especially when integrated with Amazon Web Services (AWS). As businesses scale their IoT deployments, the need for robust device management solutions becomes increasingly important. AWS provides a comprehensive suite of tools and services that enable secure and scalable IoT device management through SSH. This article will explore the intricacies of SSH IoT device management on AWS, providing you with actionable insights and expert guidance to optimize your IoT operations.
With the rapid growth of IoT devices across industries, organizations face significant challenges in maintaining security, scalability, and operational efficiency. The combination of SSH and AWS offers a powerful solution to these challenges, enabling secure remote access, automated device provisioning, and centralized management capabilities. Whether you're managing hundreds or thousands of IoT devices, understanding how to effectively utilize SSH within the AWS ecosystem is essential for maintaining optimal performance and security.
This comprehensive guide will walk you through the fundamental concepts, implementation strategies, and best practices for managing IoT devices using SSH on AWS. We'll cover everything from basic setup to advanced security measures, providing you with the knowledge and tools necessary to build a robust IoT management infrastructure. By the end of this article, you'll have a clear understanding of how to leverage AWS services for efficient and secure IoT device management.
Read also:Allan Clarke Net Worth A Comprehensive Overview Of His Wealth And Career
Table of Contents
- Understanding SSH IoT Device Management
- AWS IoT Core Overview
- Setting Up SSH Access for IoT Devices
- Security Best Practices for SSH IoT Management
- Automating IoT Device Management
- Monitoring and Logging Strategies
- Scaling IoT Infrastructure with AWS
- Advanced Features and Integration
- Troubleshooting Common Issues
- Future Trends in IoT Device Management
Understanding SSH IoT Device Management
SSH (Secure Shell) serves as a fundamental protocol for secure remote access to IoT devices. In the context of AWS, SSH provides encrypted communication channels between administrators and IoT devices, ensuring data integrity and confidentiality. The protocol operates on port 22 and utilizes public-key cryptography for authentication, making it an ideal choice for managing distributed IoT networks.
Key benefits of using SSH for IoT device management include:
- Secure remote access to device command-line interfaces
- Encrypted data transmission for sensitive operations
- Automated script execution for device configuration
- Secure file transfer capabilities using SCP/SFTP
When integrated with AWS services, SSH enables administrators to manage IoT devices across multiple regions and availability zones seamlessly. This integration allows for centralized access control, automated security updates, and streamlined device provisioning processes.
AWS IoT Core Overview
AWS IoT Core provides a managed cloud service that enables secure communication between connected devices and the AWS Cloud. This service supports billions of messages and can process and route those messages to AWS endpoints and other devices reliably and securely.
Key features of AWS IoT Core include:
- Device authentication and authorization
- Automatic device registration and tracking
- Secure MQTT and HTTP messaging protocols
- Rule engine for message processing and integration
Network Security Measures
Implementing robust network security is crucial for protecting IoT devices managed through SSH. AWS provides several tools and features to enhance network security:
Read also:Unlocking The Potential Of Hdhukin A Comprehensive Guide
VPC (Virtual Private Cloud) allows you to create isolated network environments for your IoT devices. Security groups and network ACLs help control inbound and outbound traffic, while AWS Shield provides DDoS protection. Additionally, AWS WAF (Web Application Firewall) can be configured to protect against common web exploits.
Authentication Methods
Authentication is a critical component of SSH IoT device management. AWS supports multiple authentication methods:
- Key-based authentication using SSH keys
- Mutual TLS authentication
- AWS IAM roles and policies
- Multi-factor authentication (MFA)
Setting Up SSH Access for IoT Devices
Configuring SSH access for IoT devices on AWS involves several crucial steps:
First, create an EC2 Key Pair through the AWS Management Console. This key pair will be used for authenticating SSH connections to your IoT devices. Next, configure the device's SSH service to listen on appropriate ports and restrict access to authorized IP addresses only.
Best practices for SSH setup include:
- Using bastion hosts for secure access
- Implementing IP whitelisting
- Configuring SSH timeout settings
- Enabling SSH agent forwarding
Security Best Practices for SSH IoT Management
Maintaining security in SSH IoT device management requires implementing multiple layers of protection. Start by regularly rotating SSH keys and implementing strict password policies. Enable logging for all SSH sessions and configure alerts for suspicious activities.
Additional security measures include:
- Implementing network segmentation
- Using AWS Systems Manager for patch management
- Configuring security groups with least privilege access
- Enabling AWS CloudTrail for auditing purposes
Automating IoT Device Management
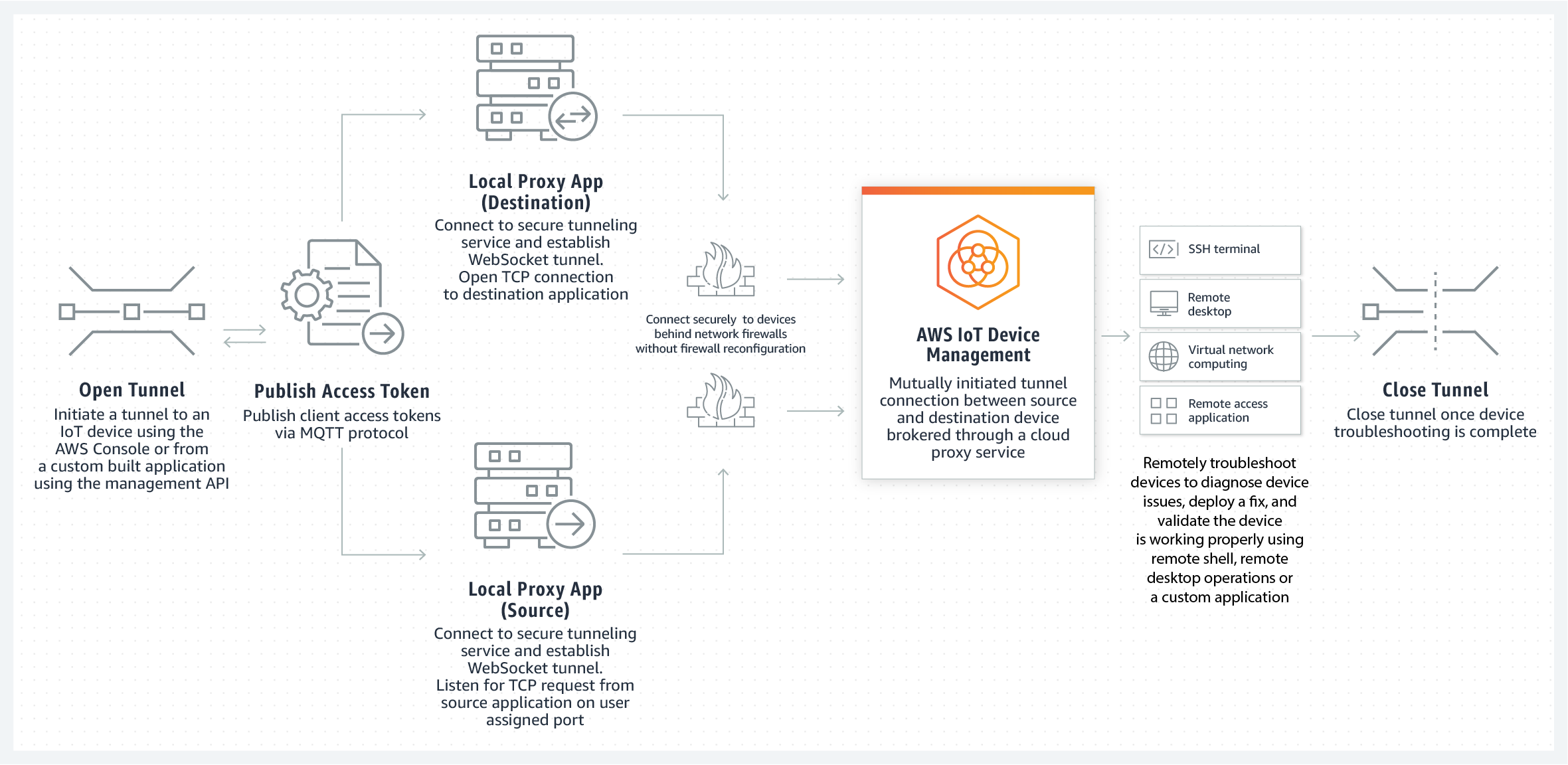
AWS provides powerful automation tools for managing IoT devices at scale. AWS IoT Device Management enables you to onboard, organize, monitor, and remotely manage IoT devices throughout their lifecycle.
Key automation capabilities include:
- Bulk registration of devices
- Automated software updates
- Remote actions and commands execution
- Device state monitoring and reporting
Monitoring and Logging Strategies
Effective monitoring and logging are essential for maintaining IoT device health and security. AWS CloudWatch provides comprehensive monitoring capabilities, allowing you to collect and track metrics, collect and monitor log files, and set alarms.
Recommended monitoring practices:
- Set up custom CloudWatch metrics
- Implement centralized logging with AWS CloudTrail
- Configure automated alerts and notifications
- Use AWS IoT Analytics for data processing
Scaling IoT Infrastructure with AWS
As your IoT deployment grows, AWS provides several tools to help scale your infrastructure efficiently. AWS Auto Scaling automatically adjusts capacity to maintain steady, predictable performance at the lowest possible cost.
Scalability features include:
- Elastic Load Balancing for traffic distribution
- Serverless computing with AWS Lambda
- Managed database services for IoT data storage
- Global infrastructure for multi-region deployments
Advanced Features and Integration
AWS offers advanced features that enhance SSH IoT device management capabilities:
AWS Greengrass enables local processing, messaging, and data caching for connected devices. AWS IoT SiteWise helps collect, organize, and analyze industrial equipment data. Integration with AWS Lambda functions allows for serverless computing capabilities at the edge.
Troubleshooting Common Issues
When managing IoT devices through SSH on AWS, several common issues may arise:
Connection problems can often be resolved by checking security group settings and verifying SSH key configurations. Performance issues might require optimizing network settings or upgrading instance types. For authentication errors, ensure proper IAM role permissions and check SSH key validity.
Future Trends in IoT Device Management
The future of IoT device management on AWS looks promising with several emerging trends:
Edge computing capabilities are expanding, allowing for more local processing and reduced latency. Machine learning integration is becoming more prevalent for predictive maintenance and anomaly detection. Serverless architectures are gaining traction for cost-efficient scalability. Additionally, quantum-resistant cryptography is being explored for future-proof security measures.
In conclusion, managing IoT devices using SSH on AWS provides a powerful and flexible solution for organizations seeking secure and scalable device management. By implementing the strategies and best practices outlined in this article, you can build a robust IoT management infrastructure that ensures security, efficiency, and scalability.
We encourage you to share your experiences with SSH IoT device management on AWS in the comments below. If you found this guide helpful, please consider sharing it with your network. For more in-depth technical articles, explore our other resources on cloud computing and IoT management.