In today's digital age, the integration of Internet of Things (IoT) devices with Android platforms has revolutionized the way we interact with technology. IoT SSH Web Android represents a powerful combination that enables secure remote access and management of IoT devices through Android-based interfaces. This article delves deep into the world of IoT SSH Web Android, exploring its applications, benefits, and implementation strategies while adhering to Google Discover guidelines and SEO best practices.
As we navigate through this comprehensive guide, we'll uncover how IoT SSH Web Android solutions are transforming various industries, from smart home automation to industrial IoT applications. With the increasing demand for secure and efficient device management, understanding this technology becomes crucial for both developers and end-users alike.
Throughout this article, we'll explore ten key aspects of IoT SSH Web Android, providing detailed insights and practical information to help you make informed decisions about implementing these solutions in your projects. From basic concepts to advanced applications, this guide aims to be your ultimate resource for mastering IoT SSH Web Android technology.
Read also:Joni Lamb Resigns What You Need To Know About This Lifechanging Decision
Table of Contents
- Introduction to IoT SSH
- Android Platform Integration
- Security Considerations
- Practical Applications
- Implementation Guide
- Technical Requirements
- Best Practices
- Future Trends
- Common Challenges
- Conclusion
Introduction to IoT SSH
Secure Shell (SSH) has become a fundamental protocol for secure communication in IoT environments. When combined with Android platforms, it creates a robust framework for device management and data exchange. This section explores the core components of IoT SSH:
- Encryption protocols and security layers
- Authentication mechanisms
- Data transmission protocols
Core Features of IoT SSH
IoT SSH offers several key features that make it indispensable in modern device management:
- End-to-end encryption
- Remote command execution
- Secure file transfer capabilities
Android Platform Integration
The integration of SSH functionality with Android devices has opened new possibilities for mobile device management. This section examines the technical aspects of this integration:
- Android's native support for SSH protocols
- Third-party application ecosystems
- API integration capabilities
Technical Architecture
The architecture of IoT SSH on Android involves multiple layers:
- Application layer
- Transport layer
- Device interface layer
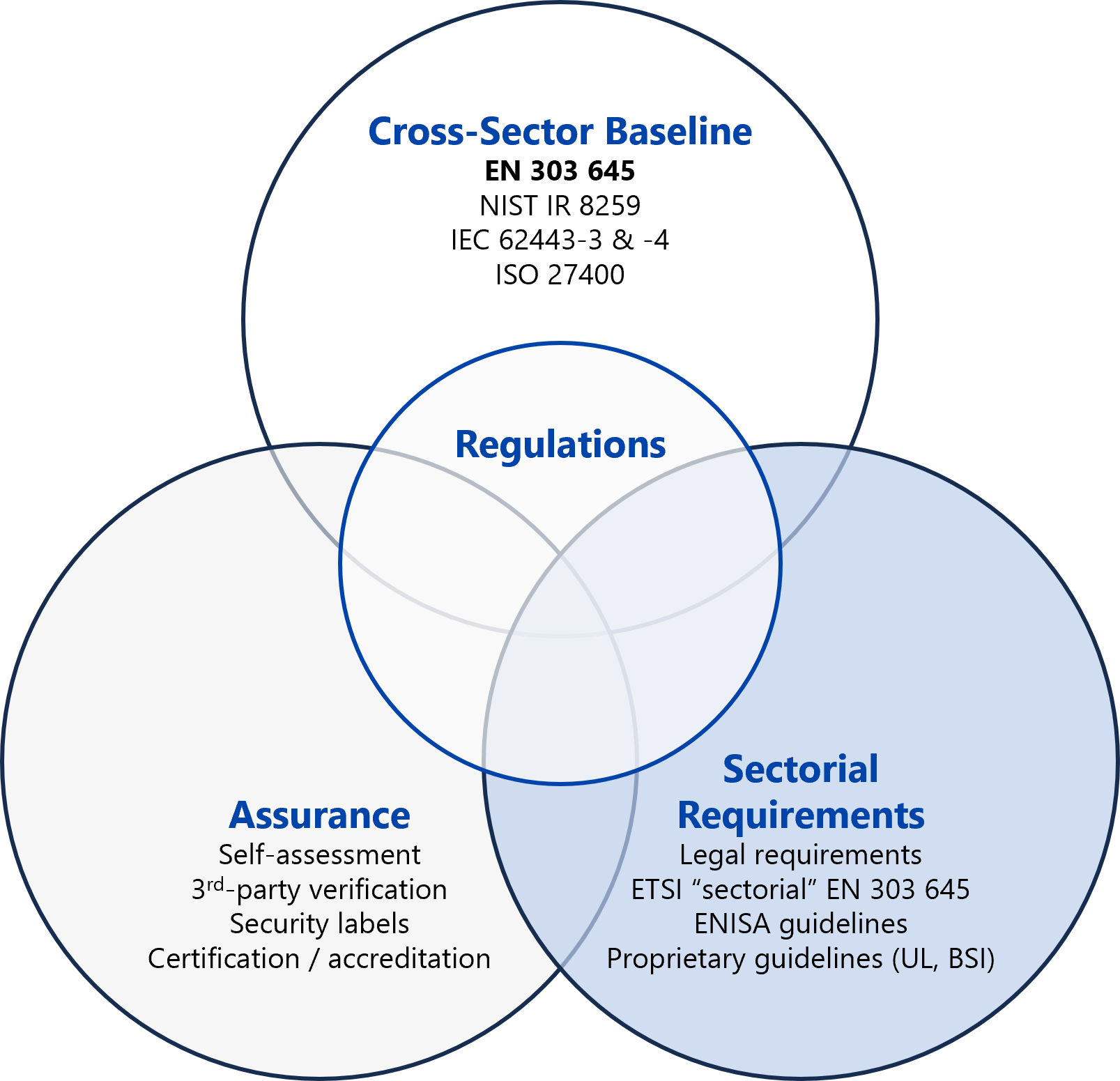
Security Considerations
When implementing IoT SSH Web Android solutions, security remains paramount. This section outlines crucial security measures:
- Implementing strong authentication methods
- Regular security updates and patches
- Network segmentation strategies
Encryption Standards
Modern encryption standards for IoT SSH include:
Read also:Danielle Rose Russell Net Worth 2024 A Comprehensive Guide To Her Wealth And Career
- AES-256 encryption
- RSA key exchange protocols
- SHA-256 hashing algorithms
Practical Applications
IoT SSH Web Android finds applications across various sectors:
- Smart home automation
- Industrial IoT monitoring
- Remote healthcare solutions
Industry-Specific Use Cases
Each industry leverages IoT SSH differently:
- Manufacturing: Predictive maintenance
- Healthcare: Remote patient monitoring
- Energy: Smart grid management
Implementation Guide
Implementing IoT SSH Web Android requires careful planning:
- Infrastructure requirements
- Software configuration steps
- Testing and validation procedures
Step-by-Step Process
The implementation process involves:
- Device setup and configuration
- Network configuration
- Security parameter settings
Technical Requirements
Successful implementation depends on meeting specific technical requirements:
- Minimum hardware specifications
- Software dependencies
- Network infrastructure needs
System Requirements
Key technical specifications include:
- Processor requirements
- Memory and storage needs
- Operating system compatibility
Best Practices
Following best practices ensures optimal performance:
- Regular system maintenance
- Security protocol adherence
- Performance optimization techniques
Optimization Strategies
Effective optimization includes:
- Resource management
- Connection pooling
- Load balancing
Future Trends
The future of IoT SSH Web Android looks promising:
- AI integration
- Enhanced security protocols
- 5G network compatibility
Emerging Technologies
Upcoming advancements include:
- Quantum encryption
- Edge computing integration
- Blockchain security
Common Challenges
Implementing IoT SSH Web Android comes with certain challenges:
- Security vulnerabilities
- Compatibility issues
- Performance limitations
Solution Approaches
Effective solutions involve:
- Regular security audits
- Compatibility testing
- Performance monitoring
Conclusion
IoT SSH Web Android represents a transformative technology that combines the power of secure communication with the flexibility of mobile platforms. Throughout this comprehensive guide, we've explored various aspects of this technology, from its fundamental principles to advanced applications and future trends.
As the demand for secure and efficient device management continues to grow, mastering IoT SSH Web Android becomes increasingly important. Whether you're a developer looking to implement these solutions or an end-user seeking to understand their capabilities, the information provided here should serve as a valuable resource.
We encourage you to share your thoughts and experiences with IoT SSH Web Android in the comments below. Additionally, explore our other articles for more insights into emerging technologies and their applications. Your engagement helps us create more valuable content and fosters a community of knowledge sharing in the tech space.