Are you looking to enhance your AWS IoT deployments with secure remote access? AWS IoT SSH Tunnel is a powerful solution that allows you to securely connect to your IoT devices and manage them remotely. In today’s interconnected world, where IoT devices are becoming increasingly critical, ensuring secure and reliable access is paramount. This article delves into the intricacies of AWS IoT SSH Tunnel, providing you with the expertise and guidance needed to implement it effectively.
As businesses adopt IoT solutions, the need for secure communication between devices and cloud platforms becomes more pressing. AWS IoT SSH Tunnel provides a robust mechanism to achieve this. By leveraging AWS’s secure infrastructure, you can establish encrypted connections to your IoT devices, ensuring data integrity and confidentiality. This guide will explore the key concepts, setup processes, and best practices to help you maximize the potential of AWS IoT SSH Tunnel.
Whether you’re a developer, IT professional, or business owner, understanding how to implement AWS IoT SSH Tunnel can significantly improve your IoT infrastructure’s security and efficiency. By the end of this article, you’ll have a clear understanding of how this technology works and how it can benefit your organization. Let’s dive into the details and uncover the full potential of AWS IoT SSH Tunnel.
Read also:Kannada Movie Movierulz A Comprehensive Guide To Streaming Kannada Cinema Online
Table of Contents
- Introduction to AWS IoT
- What is SSH Tunneling?
- Benefits of AWS IoT SSH Tunnel
- How AWS IoT SSH Tunnel Works
- Setting Up AWS IoT SSH Tunnel
- Security Best Practices for AWS IoT SSH Tunnel
- Use Cases and Applications
- Common Challenges and Solutions
- Tools and Resources for AWS IoT SSH Tunnel
- Conclusion
Introduction to AWS IoT
AWS IoT is a managed cloud service that lets connected devices easily and securely interact with cloud applications and other devices. It supports billions of devices and trillions of messages, making it a scalable solution for IoT deployments. AWS IoT provides a suite of tools and services, including device management, data processing, and analytics, to help businesses build and manage IoT applications efficiently.
One of the core components of AWS IoT is its ability to provide secure communication between devices and the cloud. AWS IoT uses MQTT, HTTP, and WebSockets protocols to facilitate communication. Additionally, it integrates seamlessly with other AWS services, such as AWS Lambda, Amazon S3, and Amazon DynamoDB, enabling developers to build robust IoT solutions.
Key Features of AWS IoT
- Device Shadow: A persistent representation of a device’s state.
- Rules Engine: Allows you to process and route data to other AWS services.
- Security: End-to-end encryption and fine-grained access control.
What is SSH Tunneling?
SSH tunneling, also known as SSH port forwarding, is a method of creating an encrypted connection between a local machine and a remote server. This technique is widely used to secure data transmission over untrusted networks. By encapsulating other network protocols within an SSH connection, SSH tunneling ensures that data remains confidential and tamper-proof.
In the context of AWS IoT, SSH tunneling can be used to securely access IoT devices located behind firewalls or NATs. This is particularly useful for remote device management, troubleshooting, and firmware updates. AWS IoT SSH Tunnel simplifies the process by automating the creation of secure tunnels, making it easier for developers to manage IoT devices.
Types of SSH Tunneling
- Local Port Forwarding: Forwards traffic from a local port to a remote server.
- Remote Port Forwarding: Forwards traffic from a remote server to a local machine.
- Dynamic Port Forwarding: Creates a SOCKS proxy for dynamic routing.
Benefits of AWS IoT SSH Tunnel
AWS IoT SSH Tunnel offers numerous advantages for businesses and developers managing IoT deployments. Below are some of the key benefits:
1. Enhanced Security
By leveraging AWS’s secure infrastructure, SSH tunnels provide end-to-end encryption, ensuring that data transmitted between devices and the cloud remains confidential. This is crucial for protecting sensitive information and complying with data privacy regulations.
Read also:Movierulz Ullu A Comprehensive Guide To Streaming And Legal Concerns
2. Simplified Remote Access
AWS IoT SSH Tunnel eliminates the need for complex network configurations, such as opening ports or configuring firewalls. This makes it easier for developers to access IoT devices remotely without compromising security.
3. Scalability
With AWS IoT’s ability to handle billions of devices, SSH tunneling can scale seamlessly to accommodate growing IoT deployments. This ensures that businesses can manage large numbers of devices efficiently.
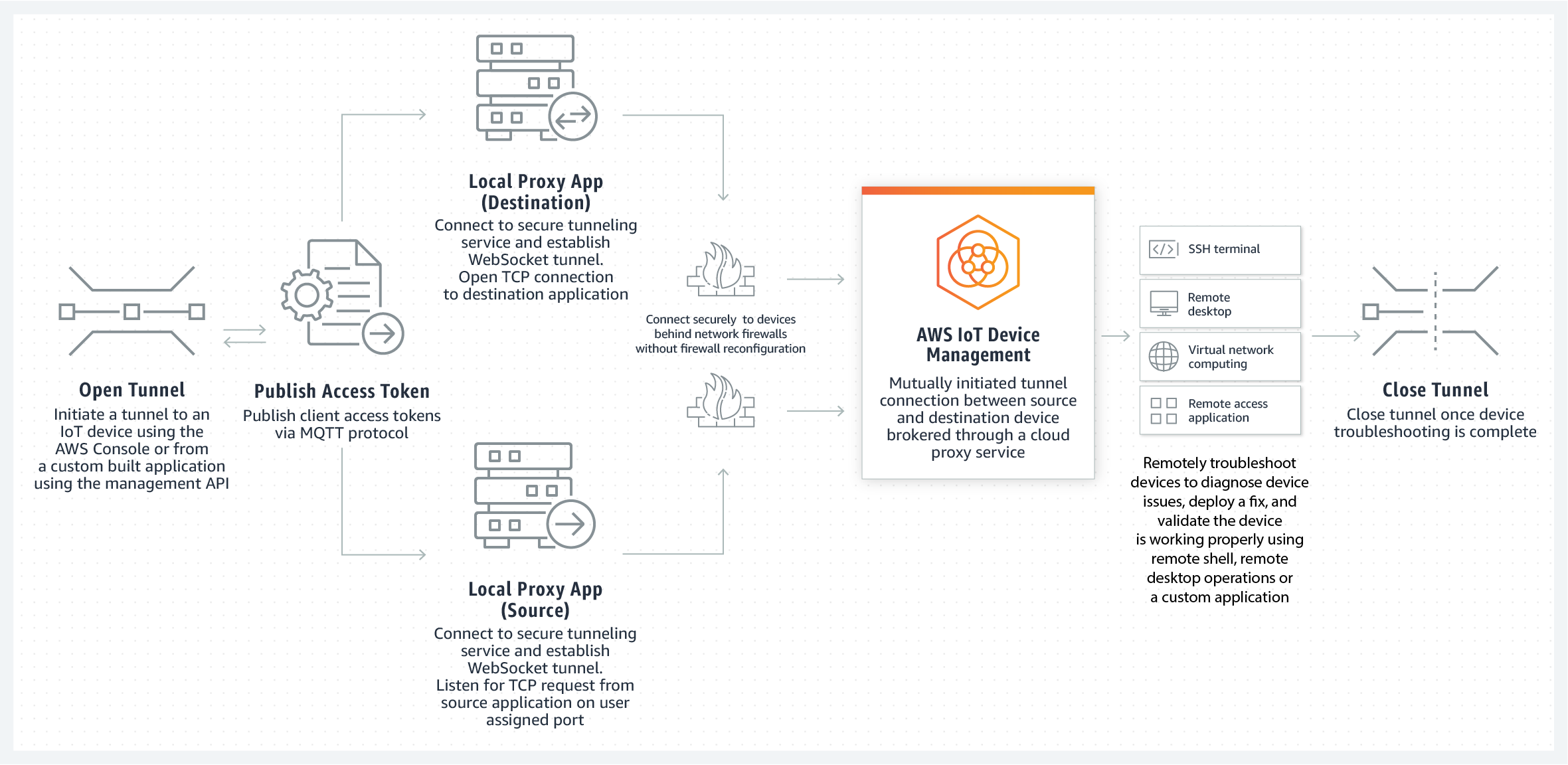
How AWS IoT SSH Tunnel Works
AWS IoT SSH Tunnel operates by creating an encrypted connection between your local machine and an IoT device via the AWS IoT Core. This process involves several key steps:
1. Device Authentication
Before establishing a tunnel, the IoT device must be authenticated using AWS IoT’s secure authentication mechanisms, such as X.509 certificates or IAM roles.
2. Tunnel Creation
Once authenticated, AWS IoT Core creates a secure tunnel between the device and the cloud. This tunnel is encrypted using SSH protocols, ensuring data integrity and confidentiality.
3. Data Transmission
Data is transmitted through the tunnel using MQTT or other supported protocols. AWS IoT Core acts as a mediator, routing data between the device and the cloud application.
Setting Up AWS IoT SSH Tunnel
Setting up AWS IoT SSH Tunnel involves several steps, including configuring your IoT devices, creating a secure tunnel, and testing the connection. Below is a step-by-step guide:
1. Prerequisites
- An AWS account with access to AWS IoT Core.
- AWS CLI installed and configured on your local machine.
- IoT devices registered in AWS IoT Core.
2. Registering IoT Devices
Use the AWS Management Console or CLI to register your IoT devices. Each device must have a unique identifier and authentication credentials.
3. Creating a Secure Tunnel
Use the AWS CLI to create a secure tunnel. The command typically looks like this:
aws iotsecuretunneling open-tunnel --destination-config '{"thingName":"your-thing-name"}'4. Testing the Connection
Once the tunnel is created, use an SSH client to connect to the device. Verify that the connection is secure and data is transmitted correctly.
Security Best Practices for AWS IoT SSH Tunnel
To ensure the security of your AWS IoT SSH Tunnel, follow these best practices:
1. Use Strong Authentication
Always use strong authentication mechanisms, such as X.509 certificates or IAM roles, to secure your IoT devices.
2. Regularly Update Firmware
Keep your IoT devices’ firmware up to date to protect against vulnerabilities.
3. Monitor and Audit
Use AWS CloudTrail and AWS IoT Device Defender to monitor and audit your IoT deployments for suspicious activity.
Use Cases and Applications
AWS IoT SSH Tunnel has a wide range of applications across various industries. Below are some common use cases:
1. Remote Device Management
Enable IT teams to manage IoT devices remotely, reducing the need for on-site visits.
2. Firmware Updates
Securely deploy firmware updates to IoT devices without exposing them to the public internet.
3. Troubleshooting
Access IoT devices for troubleshooting and diagnostics without compromising security.
Common Challenges and Solutions
While AWS IoT SSH Tunnel offers numerous benefits, there are some challenges to be aware of:
1. Network Latency
High latency can affect the performance of SSH tunnels. Use AWS Global Accelerator to reduce latency.
2. Device Compatibility
Ensure that your IoT devices support SSH tunneling protocols. If not, consider using a gateway device.
Tools and Resources for AWS IoT SSH Tunnel
Here are some tools and resources to help you get started with AWS IoT SSH Tunnel:
Conclusion
AWS IoT SSH Tunnel is a powerful tool for securely managing IoT devices and ensuring reliable communication between devices and the cloud. By leveraging AWS’s robust infrastructure, you can enhance the security, scalability, and efficiency of your IoT deployments. Whether you’re troubleshooting devices, deploying firmware updates, or managing remote access, AWS IoT SSH Tunnel provides a reliable solution.
We hope this guide has provided you with valuable insights into AWS IoT SSH Tunnel. If you have any questions or need further assistance, feel free to leave a comment below. Don’t forget to share this article with your colleagues and explore other resources on our site to deepen your understanding of AWS IoT and related technologies.