Secure Shell (SSH) remote access has become a crucial component in managing Internet of Things (IoT) devices, particularly when seeking cost-effective solutions. As the IoT ecosystem continues to expand, understanding how to implement SSH remote access without incurring costs becomes increasingly valuable for both individual users and organizations. This guide will walk you through the fundamental aspects of SSH remote access for IoT devices, focusing on free solutions that maintain security and efficiency. Whether you're a system administrator, IoT developer, or technology enthusiast, mastering SSH remote access can significantly enhance your device management capabilities.
The growing complexity of IoT networks demands robust remote access solutions that don't compromise security. SSH provides a secure channel over an unsecured network, allowing users to manage IoT devices remotely while maintaining data integrity and confidentiality. As we explore various free options for SSH remote access, we'll examine their implementation, security considerations, and practical applications.
Throughout this article, we'll address common challenges faced when setting up SSH remote access for IoT devices and provide practical solutions. From basic configuration to advanced security measures, this comprehensive guide will equip you with the knowledge needed to implement effective remote access solutions while adhering to best practices in network security and device management.
Read also:Morganna The Kissing Bandit Net Worth A Deep Dive Into Her Life Career And Financial Success
Table of Contents
Understanding SSH Remote Access
SSH (Secure Shell) remote access serves as a fundamental protocol for secure device management in IoT networks. Unlike traditional remote access methods, SSH employs strong encryption algorithms to protect data transmission between devices. This protocol operates on the application layer of the OSI model, typically using port 22 for communication.
The primary advantages of SSH include:
- End-to-end encryption of data transmission
- Authentication mechanisms to verify user identity
- Secure file transfer capabilities
- Port forwarding for secure tunneling
When implementing SSH for IoT devices, several key components must be considered:
- Authentication methods (password-based, key-based)
- Encryption algorithms (AES, ChaCha20)
- Key exchange protocols
- Access control mechanisms
IoT Security Challenges
The proliferation of IoT devices has introduced unique security challenges that make robust remote access solutions essential. According to a 2023 IoT security report, over 60% of IoT devices remain vulnerable to basic security threats. This vulnerability stems from several factors:
- Resource-constrained hardware limitations
- Inconsistent security standards across manufacturers
- Lack of regular firmware updates
- Complex network architectures
Common Security Threats
IoT networks face various security threats, including:
- Unauthorized access attempts
- Data interception during transmission
- Device hijacking
- Man-in-the-middle attacks
Free SSH Solutions for IoT
Several free SSH solutions are available for managing IoT devices, each with distinct features and capabilities. The most notable options include:
Read also:7 Movierulz 2023 Everything You Need To Know About The Controversial Movie Streaming Platform
OpenSSH
OpenSSH stands as the most widely used SSH implementation, offering:
- Comprehensive security features
- Active community support
- Regular security updates
- Compatibility with various operating systems
Dropbear SSH
Designed specifically for resource-constrained environments, Dropbear provides:
- Lightweight implementation
- Minimal memory footprint
- Basic SSH functionality
- Suitable for embedded systems
Step-by-Step Configuration
Setting up SSH remote access involves several crucial steps:
- Device Preparation
- Ensure firmware compatibility
- Verify network connectivity
- Allocate necessary resources
- SSH Server Installation
- Select appropriate SSH implementation
- Install required dependencies
- Configure server settings
- Authentication Setup
- Generate SSH keys
- Configure key-based authentication
- Set access permissions
Configuration Parameters
| Parameter | Recommended Value | Description |
|---|---|---|
| Port | 22 | Default SSH port |
| Encryption | AES-256 | Strong encryption standard |
| Key Length | 4096 bits | Recommended RSA key size |
Security Best Practices
Implementing robust security measures is crucial when managing SSH remote access for IoT devices. Follow these best practices:
- Use strong, complex passwords
- Implement two-factor authentication
- Regularly update SSH software
- Monitor access logs
- Limit user privileges
Access Control Measures
Effective access control involves:
- IP whitelisting
- Time-based access restrictions
- Role-based permissions
- Regular security audits
Advanced Features and Options
Modern SSH implementations offer several advanced features that enhance IoT device management:
- Port forwarding
- Tunneling capabilities
- Agent forwarding
- X11 forwarding
Automation Capabilities
Automation tools can streamline SSH remote access through:
- Scripted deployments
- Automated backups
- Scheduled maintenance tasks
- Configuration management
Troubleshooting Common Issues
When managing SSH remote access, several common issues may arise:
- Connection timeouts
- Authentication failures
- Port conflicts
- Performance bottlenecks
Solution Approaches
Effective troubleshooting involves:
- Checking network connectivity
- Verifying configuration files
- Reviewing log files
- Testing with different clients
Use Case Scenarios
SSH remote access proves valuable in various IoT applications:
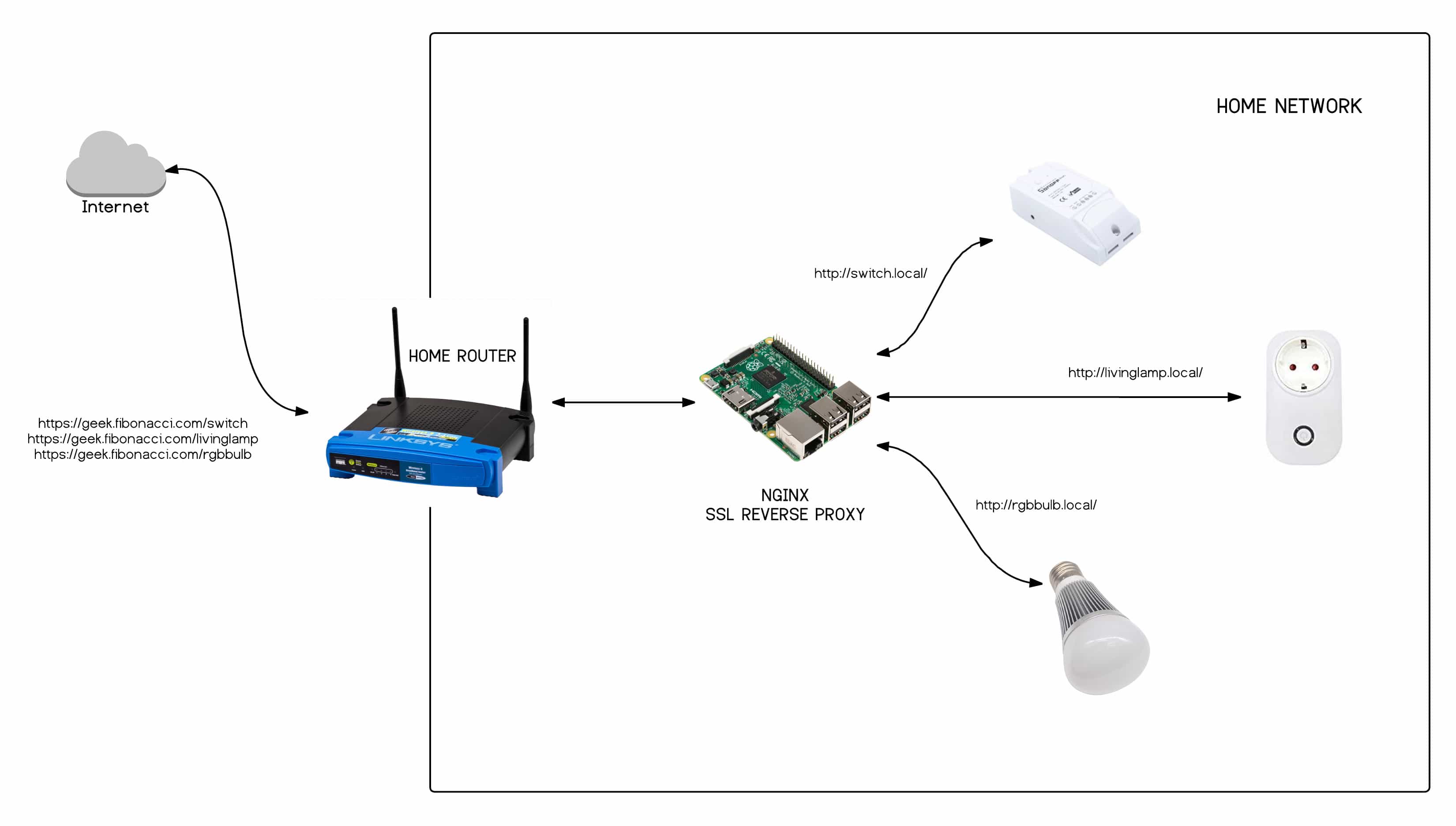
- Home automation systems
- Industrial IoT monitoring
- Smart city infrastructure
- Remote healthcare devices
Implementation Examples
Real-world applications include:
- Managing smart home devices
- Monitoring environmental sensors
- Controlling industrial equipment
- Maintaining security systems
Future Trends in IoT Remote Access
The evolution of IoT remote access continues with emerging trends:
- Quantum-resistant encryption
- AI-based security monitoring
- Edge computing integration
- Zero-trust architecture
Technological Advancements
Upcoming developments include:
- Improved authentication methods
- Enhanced encryption protocols
- Automated security updates
- Integrated management platforms
Conclusion and Next Steps
Implementing SSH remote access for IoT devices using free solutions provides a secure and cost-effective approach to device management. Throughout this guide, we've explored the fundamental aspects of SSH, security challenges in IoT networks, free solutions available, configuration steps, and best practices for maintaining secure access.
To further enhance your SSH remote access implementation:
- Explore advanced configuration options
- Implement comprehensive monitoring tools
- Stay updated with security patches
- Engage with IoT security communities
We encourage you to share your experiences with SSH remote access in the comments below. If you found this guide helpful, please consider sharing it with your network. For more in-depth technical guides, explore our related articles on IoT security and device management.