Managing IoT devices securely is crucial in today's interconnected world. One of the most effective methods to ensure secure communication with your IoT devices is through SSH (Secure Shell) remote access. This tutorial will guide you through the process of setting up and managing remote SSH connections while implementing robust firewall protection. As IoT devices continue to proliferate across various industries, understanding how to establish secure connections becomes increasingly vital for both individual users and organizations.
The combination of remote SSH access and proper firewall configuration provides a powerful solution for managing IoT devices safely. With cyber threats becoming more sophisticated, it's essential to implement security measures that protect your devices from unauthorized access while maintaining convenient remote management capabilities. This guide will walk you through the entire process, from basic setup to advanced security configurations.
Whether you're a home user managing smart devices or an IT professional overseeing industrial IoT systems, mastering remote SSH and firewall management is crucial. We'll explore not only the technical aspects but also best practices for maintaining security while ensuring optimal device performance. By the end of this tutorial, you'll have a comprehensive understanding of how to implement secure remote access for your IoT infrastructure.
Read also:Dr Doom Technology The Future Of Innovation And Digital Transformation
Table of Contents
Understanding SSH Protocol
Secure Shell (SSH) is a cryptographic network protocol that provides secure communication over unsecured networks. It was first developed in 1995 by Tatu Ylönen as a response to growing security concerns in remote system administration. The current version, SSH-2, offers enhanced security features and better performance compared to its predecessor.
SSH operates on the client-server model, where the client initiates a connection to the server. The protocol uses strong encryption algorithms to secure data transmission, including AES, ChaCha20, and various hashing functions. This encryption ensures that both authentication credentials and data transfer remain protected from interception or tampering.
Key features of SSH include:
- Secure remote login capabilities
- File transfer through SCP and SFTP protocols
- Port forwarding for secure tunneling
- X11 forwarding for remote graphical applications
These features make SSH an indispensable tool for managing IoT devices across different network environments.
IoT Security Challenges
The Internet of Things presents unique security challenges due to its diverse ecosystem and widespread deployment. Recent studies indicate that over 50% of IoT devices contain vulnerabilities that could be exploited by attackers. These vulnerabilities often stem from:
- Inadequate default security settings
- Lack of regular firmware updates
- Insufficient authentication mechanisms
These challenges highlight the importance of implementing robust security measures when managing IoT infrastructure.
Read also:Tyler Henry Net Worth 2024 A Comprehensive Guide To His Wealth And Career
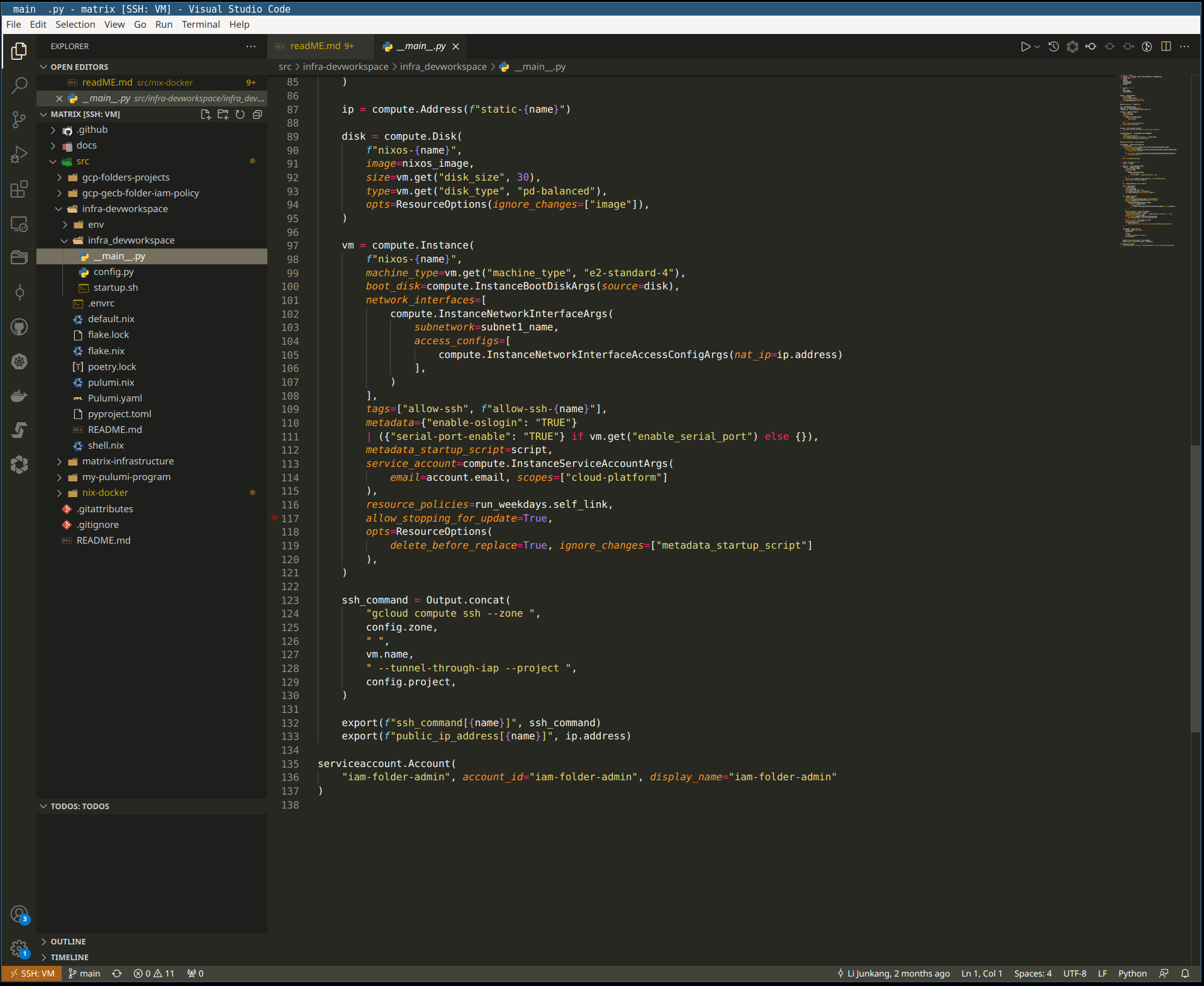
Setting Up SSH for Remote Access
Proper SSH setup is crucial for establishing secure connections with IoT devices. The process involves multiple steps that ensure both functionality and security.
SSH Installation Process
Installing SSH on IoT devices typically follows these steps:
- Verify device compatibility with SSH protocol
- Install necessary SSH packages using package managers
- Configure initial server settings through configuration files
Most Linux-based IoT devices use OpenSSH as their default SSH implementation, which provides comprehensive documentation and community support.
Basic Configuration Steps
After installation, basic configuration includes:
- Changing default port numbers
- Implementing key-based authentication
- Setting up proper user permissions
These configurations help mitigate common attack vectors and enhance overall security.
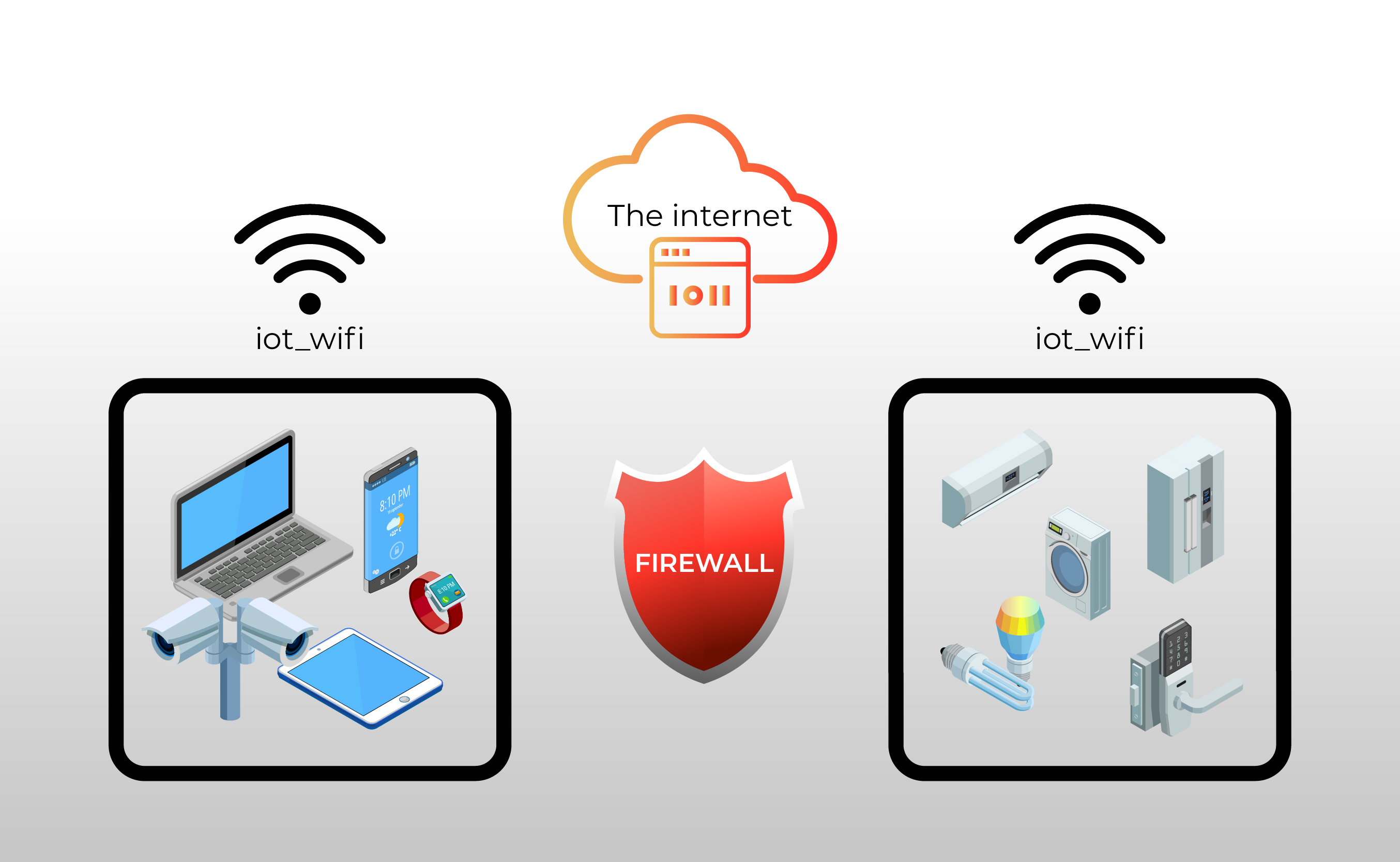
Firewall Fundamentals for IoT
Firewalls serve as crucial protection layers for IoT devices, controlling incoming and outgoing network traffic based on predetermined security rules. Modern firewalls offer various features specifically designed for IoT environments, including:
- Stateful packet inspection
- Intrusion detection and prevention systems
- Application-layer filtering
Proper firewall configuration can significantly reduce the attack surface of IoT devices.
Advanced Security Measures
Implementing advanced security measures helps protect IoT devices from sophisticated threats. Key strategies include:
- Two-factor authentication (2FA) implementation
- Regular security audits and vulnerability assessments
- Network segmentation for IoT devices
These measures, combined with proper SSH configuration, create multiple layers of security that significantly enhance device protection.
Troubleshooting Common Issues
Despite careful setup, users may encounter various issues with SSH connections. Common problems include:
- Connection timeouts due to network configuration
- Authentication failures from incorrect key setup
- Firewall blocking legitimate traffic
Proper troubleshooting methodology involves systematic diagnosis and resolution of these issues while maintaining security integrity.
Best Practices for Remote Management
Following best practices ensures both security and efficiency in managing IoT devices remotely:
- Regularly update SSH software and device firmware
- Implement strict access control policies
- Maintain detailed logs of all remote access attempts
These practices help maintain a secure and reliable remote management system.
Essential Tools and Resources
Several tools and resources can enhance SSH and firewall management:
- Fail2Ban for intrusion prevention
- UFW (Uncomplicated Firewall) for simplified configuration
- SSHGuard for protection against brute-force attacks
These tools complement basic SSH and firewall configurations, providing additional layers of security.
Future Trends in IoT Security
The landscape of IoT security continues to evolve with emerging technologies:
- AI-powered threat detection systems
- Quantum-resistant encryption methods
- Blockchain-based authentication protocols
These advancements promise to enhance the security and reliability of remote IoT management systems.
Conclusion
This comprehensive guide has covered essential aspects of remote SSH IoT firewall management, from basic setup to advanced security measures. By implementing the discussed techniques and best practices, you can significantly enhance the security of your IoT infrastructure while maintaining convenient remote access capabilities.
We encourage you to apply these methods to your IoT management strategy and share your experiences. If you found this tutorial helpful, please consider sharing it with others who might benefit from this information. For more in-depth guides and technical resources, explore our other articles covering various aspects of IoT security and management.